Benchmarking Computational Methods: A Framework for Assessing Accuracy and Reliability in Drug Discovery
This article provides a comprehensive framework for benchmarking the accuracy of computational methods in drug discovery, addressing a critical need for standardized assessment.
Benchmarking Computational Methods: A Framework for Assessing Accuracy and Reliability in Drug Discovery
Abstract
This article provides a comprehensive framework for benchmarking the accuracy of computational methods in drug discovery, addressing a critical need for standardized assessment. Aimed at researchers and development professionals, it explores the foundational principles of benchmarking, reviews current methodological applications from QSAR to AI, outlines common pitfalls and optimization strategies, and establishes robust protocols for validation and comparative analysis. By synthesizing insights from recent studies and established guidelines, the content offers practical direction for selecting, validating, and improving computational tools to enhance the reliability of predictions in biomedical research.
The Critical Need for Benchmarking: Establishing Standards in Computational Drug Discovery
In computational biology and other data-driven sciences, researchers are frequently faced with a choice between numerous methods for performing data analyses. This decision is critical, as method selection can significantly affect scientific conclusions and subsequent research directions [1]. The rapid expansion of computational techniques, with nearly 400 methods available for analyzing data from single-cell RNA-sequencing experiments at the time of one review, presents both an opportunity and a challenge [1]. Within this context, reproducibility—specifically defined in genomics as the ability of bioinformatics tools to maintain consistent results across technical replicates—emerges as a fundamental problem that threatens scientific progress [2]. This article argues that rigorous, neutral benchmarking is non-negotiable for addressing this reproducibility crisis, with a specific focus on its critical role in evaluating DOS (Denial of Service) accuracy across computational methods in cybersecurity research.
The Reproducibility Crisis in Computational Science
Defining Reproducibility in Computational Contexts
In computational research, reproducibility and related concepts like replicability and robustness are often defined based on whether identical code and data are used [2]. Goodman et al. define methods reproducibility as the ability to precisely repeat experimental and computational procedures using the same data and tools to yield identical results [2]. In genomics, this translates to obtaining consistent outcomes across multiple runs of bioinformatics tools using the same parameters and genomic data [2].
The challenge extends to cybersecurity research, where computational methods must reliably detect and classify attacks such as Denial of Service (DoS), Distributed Denial of Service (DDoS), and Mirai attacks in IoT environments [3]. Variations in algorithm implementation, parameter settings, and data processing approaches can significantly impact the reproducibility of results, potentially leading to inconsistent security recommendations and vulnerable systems.
Bioinformatics tools can introduce both deterministic and stochastic variations that compromise reproducibility [2]. Deterministic variations include algorithmic biases, such as reference bias in alignment algorithms favoring sequences containing reference alleles [2]. Stochastic variations stem from intrinsic randomness in computational processes like Markov Chain Monte Carlo and genetic algorithms [2]. These variations can produce divergent outcomes even when analyzing identical datasets under identical conditions.
In cybersecurity, similar challenges exist where machine learning models for attack classification may produce inconsistent results due to variations in feature selection methods, data preprocessing techniques, or random initialization of algorithm parameters [3].
Benchmarking as the Cornerstone of Reproducibility
The Essential Role of Benchmarking
Benchmarking studies aim to rigorously compare the performance of different methods using well-characterized benchmark datasets to determine method strengths and provide recommendations for method selection [1]. Properly designed benchmarking serves as a crucial mechanism for:
- Identifying performance gaps between existing methods and ideal outcomes [4]
- Driving continuous improvement in method development and implementation [4]
- Establishing reliable standards for evaluating methodological claims [1]
- Enhancing competitive advantage for organizations implementing best practices [4]
Types of Benchmarking Studies
Benchmarking in computational sciences generally falls into three broad categories [1]:
- Method development benchmarks: Performed by method developers to demonstrate the merits of their new approach
- Neutral benchmarks: Conducted independently of method development by authors without perceived bias
- Community challenges: Organized initiatives such as those from DREAM, CAMI, and MAQC/SEQC consortia [1]
Neutral benchmarking studies are particularly valuable for the research community as they focus specifically on comparison rather than promoting a particular method [1].
Designing Rigorous Benchmarking Studies for DOS Accuracy
Defining Purpose and Scope
The purpose and scope of a benchmark should be clearly defined at the beginning of the study, as this fundamentally guides the design and implementation [1]. For DOS accuracy evaluation, this might include determining whether the focus is on detection sensitivity, classification accuracy, computational efficiency, or all these factors. The scope decision involves tradeoffs in terms of available resources, with neutral benchmarks ideally being as comprehensive as possible [1].
Selection of Methods
The selection of methods for benchmarking should be guided by the study's purpose and scope [1]. A comprehensive neutral benchmark should include all available methods for a specific type of analysis, while benchmarks for new method development may sufficiently compare against a representative subset of state-of-the-art and baseline methods [1]. Inclusion criteria should be chosen without favoring any methods, and exclusion of widely used methods should be justified [1].
Selection and Design of Datasets
The selection of reference datasets represents a critical design choice in benchmarking [1]. For DOS accuracy research, this typically involves using well-characterized datasets such as CICDDoS2019, CICIoT2023, or Edge-IIoT [3] [5]. These datasets can include both simulated data with known "ground truth" and real-world experimental data capturing actual attack patterns [1] [3]. Including a variety of datasets ensures methods can be evaluated under a wide range of conditions [1].
Establishing Evaluation Criteria
A robust benchmarking study employs multiple evaluation criteria to assess different aspects of performance. For DOS accuracy research, key quantitative metrics typically include [3]:
- Accuracy: Overall correctness of the classification
- Precision: Proportion of true positives among all positive predictions
- Sensitivity/Recall: Ability to identify all actual attacks
- F1-Score: Harmonic mean of precision and recall
- Computational Efficiency: Training and prediction times
Secondary measures might include scalability, resource requirements, and usability factors [1] [3].
Experimental Protocol for Benchmarking DOS Detection Methods
Methodology for Comprehensive Evaluation
Based on established benchmarking principles and recent studies in IoT security, the following experimental protocol provides a framework for evaluating DOS accuracy across computational methods:
Data Preprocessing: Address class imbalance techniques such as undersampling to prevent model bias [3]. Normalize features to ensure consistent scaling across the dataset.
Feature Selection: Implement multiple feature selection methods to compare their impact, including:
Model Training: Apply multiple machine learning algorithms to ensure comprehensive comparison, including Random Forest, Gradient Boosting, Naive Bayes, Decision Tree, and K-Nearest Neighbors [3]. Utilize cross-validation techniques to prevent overfitting.
Performance Evaluation: Measure all key metrics (accuracy, precision, sensitivity, F1-score) consistently across all methods and configurations [3]. Record computational efficiency metrics including training time and prediction time [3].
Statistical Analysis: Conduct significance testing to determine whether observed performance differences are statistically meaningful rather than incidental.
Research Reagent Solutions for DOS Detection Benchmarking
Table: Essential Components for DOS Detection Experiments
| Research Reagent | Function | Example Specifications |
|---|---|---|
| Benchmark Datasets | Provide standardized data for training and evaluation | CICIoT2023, CICDDoS2019, Edge-IIoT [3] [5] |
| Feature Selection Algorithms | Identify most relevant features for classification | Chi-square, PCA, Random Forest Regressor [3] |
| Machine Learning Libraries | Implement classification algorithms | Scikit-learn, TensorFlow, PyTorch |
| Performance Metrics | Quantify detection accuracy and efficiency | Accuracy, Precision, F1-Score, Training Time [3] |
| Computational Environment | Standardize hardware/software configuration | CPU/GPU specifications, memory capacity, operating system |
Workflow for Comprehensive Benchmarking
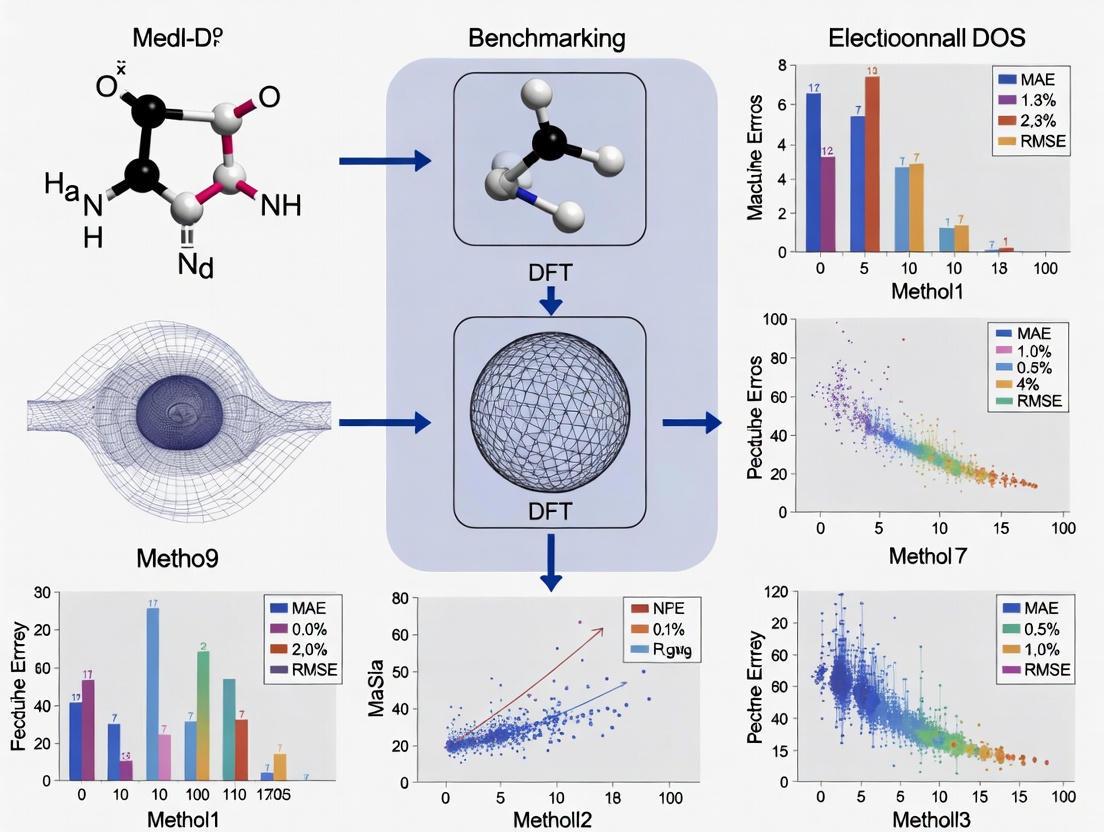
The following diagram illustrates the systematic workflow for conducting a rigorous benchmarking study of DOS detection methods:
Diagram: Benchmarking Workflow for DOS Accuracy Evaluation
Quantitative Results: Benchmarking DOS Detection Performance
Performance Comparison Across Machine Learning Algorithms
Table: Performance Metrics for DOS Detection Using Different Feature Selection Methods (Based on CICIoT2023 Dataset)
| Machine Learning Algorithm | Feature Selection Method | Accuracy (%) | Precision (%) | Sensitivity (%) | F1-Score (%) | Training Time Reduction* |
|---|---|---|---|---|---|---|
| Random Forest | Random Forest Regressor | 99.99 | 99.98 | 99.99 | 99.99 | 96.42% |
| Decision Tree | Random Forest Regressor | 99.99 | 99.97 | 99.98 | 99.98 | 98.71% |
| Gradient Boosting | Random Forest Regressor | 99.99 | 99.96 | 99.97 | 99.97 | 95.88% |
| K-Nearest Neighbors | Chi-square | 99.12 | 98.95 | 98.87 | 98.91 | 92.15% |
| Naive Bayes | PCA | 98.76 | 98.34 | 98.25 | 98.29 | 97.43% |
Note: Training time reduction compared to previously reported results in existing literature [3]
Comparative Analysis of Feature Selection Methods
Table: Impact of Feature Selection on DOS Classification Performance
| Feature Selection Method | Best-Performing Algorithm | Accuracy Achieved | Key Advantages | Computational Efficiency |
|---|---|---|---|---|
| Random Forest Regressor (RFR) | Random Forest | 99.99% | Identifies non-linear relationships, handles mixed data types | Moderate training time, fast inference |
| Chi-square | K-Nearest Neighbors | 99.12% | Computational efficiency, simple implementation | Fast execution, minimal overhead |
| Principal Component Analysis (PCA) | Naive Bayes | 98.76% | Dimensionality reduction, handles correlated features | Moderate execution time |
Analysis of Benchmarking Results for DOS Accuracy
Interpretation of Quantitative Findings
The benchmarking results demonstrate that traditional machine learning algorithms like Random Forest, Decision Tree, and Gradient Boosting can achieve exceptional accuracy (99.99%) in classifying DOS, DDoS, and Mirai attacks when paired with appropriate feature selection methods [3]. The Random Forest Regressor feature selection method consistently outperformed other approaches across multiple algorithms [3].
A critical finding from benchmarking studies is the tradeoff between accuracy and computational efficiency. While multiple algorithms achieved similar accuracy levels, the Decision Tree model demonstrated remarkable efficiency improvements with a 98.71% reduction in training time and a 99.53% reduction in prediction time compared to previously reported results [3]. This highlights the importance of including computational efficiency metrics alongside accuracy measures in benchmarking studies, particularly for resource-constrained IoT environments [3].
Challenges in Attack Classification
Benchmarking studies reveal inherent challenges in distinguishing between certain attack types. DOS and DDoS attacks present particular classification difficulties due to their shared network traffic characteristics [3]. In contrast, Mirai attacks are generally well-classified because of their distinct operational patterns [3]. These findings underscore how rigorous benchmarking can identify not just overall performance but also specific strengths and limitations of methods across different attack scenarios.
Visualization Framework for Benchmarking Analysis
Data Visualization Best Practices for Benchmarking Studies
Effective visualization of benchmarking results enhances interpretation and communication of findings. The following principles should guide visualization design [6]:
- Know your audience: Tailor visualizations to researchers, scientists, and drug development professionals
- Focus on the core message: Highlight key comparisons and performance differences
- Select appropriate visual encodings: Match visual representations to data types and relationships
- Use color effectively: Implement color palettes that enhance comprehension
- Avoid chartjunk: Eliminate unnecessary visual elements that don't convey information
Color Palette for Benchmarking Visualizations
Table: Recommended Color Palette for Data Visualizations
| Color Hex Code | Recommended Usage | Accessibility Considerations |
|---|---|---|
| #4285F4 | Primary data series, key metrics | Sufficient contrast against white backgrounds |
| #EA4335 | Highlighting performance gaps, anomalies | Meets enhanced contrast requirements [7] |
| #FBBC05 | Secondary data series, comparisons | Avoid with light backgrounds for text |
| #34A853 | Positive outcomes, best performers | Paired with dark text for labels |
| #FFFFFF | Background color | Provides clean canvas for data presentation |
| #F1F3F4 | Alternate backgrounds, gridlines | Subtle distinction from white |
| #202124 | Primary text, labels | Excellent readability on light backgrounds |
| #5F6368 | Secondary text, axis labels | Meets minimum contrast ratios [7] |
Performance Evaluation Framework
The following diagram illustrates the multi-dimensional evaluation framework necessary for comprehensive benchmarking of DOS detection methods:
Diagram: Multi-dimensional Evaluation Framework for DOS Detection
The reproducibility crisis in computational science represents a fundamental challenge to scientific progress, particularly in critical areas like DOS attack detection where accuracy directly impacts security outcomes. Through systematic examination of benchmarking methodologies and experimental results, this review demonstrates that rigorous benchmarking is non-negotiable for establishing reliable, reproducible computational methods.
The framework presented—encompassing careful scope definition, comprehensive method selection, appropriate dataset choice, and multi-dimensional evaluation criteria—provides a roadmap for conducting benchmarking studies that yield meaningful, actionable insights. As computational methods continue to evolve and proliferate, the scientific community must prioritize neutral benchmarking initiatives that objectively assess performance across diverse scenarios and requirements.
For researchers, scientists, and drug development professionals relying on computational methods, the implications are clear: benchmarking should be integrated as a fundamental component of method selection and validation processes. Only through such rigorous comparative evaluation can we advance toward truly reproducible computational science that generates reliable knowledge and drives meaningful innovation.
In computational research, the reliability of a model is governed by three foundational pillars: accuracy, bias, and applicability domain. Accuracy quantifies a model's predictive performance on a given task, often measured by metrics such as F1-score or area under the curve (AUC). Bias describes systematic errors that skew predictions, frequently arising from non-representative training data. The applicability domain (AD) defines the boundary within the chemical, biological, or feature space where the model's predictions are reliable; predictions for samples outside this domain are considered uncertain [8]. In the context of drug response prediction (DRP) and intrusion detection systems (IDS), rigorously defining these concepts is paramount for translating computational models into real-world applications. Benchmarking studies reveal a critical challenge: models that exhibit high accuracy on their native dataset often suffer significant performance drops when applied to external datasets, highlighting the limitations of internal validation and the necessity of cross-dataset generalization analysis [9]. This guide objectively compares the performance of various computational methods, detailing the experimental protocols and data that underpin these core concepts.
Experimental Protocols for Benchmarking
Standardized benchmarking requires rigorous, reproducible methodologies. The following protocols are commonly employed in computational research.
Cross-Dataset Generalization Analysis
This protocol tests a model's robustness and generalizability by training it on one dataset and evaluating it on a completely separate, unseen dataset.
- Objective: To assess real-world applicability and prevent over-optimistic performance estimates from internal cross-validation.
- Workflow: The process involves using a benchmark dataset composed of multiple source studies (e.g., CCLE, CTRPv2, GDSCv1 for DRP). Models are trained on the training split of a source dataset. The trained model is then used to make predictions on the test splits of all other target datasets without any retraining. Performance is measured on all these external tests [9].
- Key Output: Generalization metrics that quantify the performance drop from source to target datasets.
Defining the Applicability Domain
The Applicability Domain (AD) is defined using measures that reflect the reliability of individual predictions. These measures fall into two main categories:
- Novelty Detection: This approach flags objects that are unusual or dissimilar to the training set objects in terms of their explanatory variables (e.g., molecular descriptors). It is independent of the underlying classifier and relies on one-class classification to define a region of "known" objects [8]. Common methods include various distance measures to the training data.
- Confidence Estimation: This approach uses information from the trained classifier itself, most effectively through class probability estimates. A future object's distance to the decision boundary is a strong predictor of its probability of misclassification. Benchmarks have shown that class probability estimates consistently perform best at differentiating reliable from unreliable predictions [8]. Ensemble methods, like Random Forests, naturally provide a confidence score through the fraction of votes for a predicted class.
Handling Class Imbalance and Data Preprocessing
For classification tasks, especially in intrusion detection, sophisticated preprocessing is critical.
- Class Imbalance: Techniques like SMOTE (Synthetic Minority Over-sampling Technique) are used to generate synthetic samples for the minority class, preventing model bias toward the majority class [10].
- Feature Skewness: Applying transformations such as the Quantile Uniform Transformation reduces feature skewness while preserving critical patterns (e.g., attack signatures in security data). This has been shown to achieve near-zero skewness (0.0003), outperforming log transformations (1.8642 skewness) [10].
- Feature Selection: A multi-layered approach combining correlation analysis, Chi-square statistics with p-value validation, and feature dependency examination enhances model discriminative power and efficiency [10].
Performance Comparison of Computational Methods
Performance in Intrusion Detection Systems
Table 1: Performance comparison of machine learning models for DDoS attack detection on various datasets.
| Model | Dataset | Accuracy (%) | Precision (%) | F1-Score (%) | Notes |
|---|---|---|---|---|---|
| Random Forest (RF) | CICIDS2017 | 98.9 | - | - | PCA-based feature selection [11] |
| Random Forest (RF) | CICDDoS2019 | 98.7 | - | - | PCA-based feature selection [11] |
| SVM | CICIDS2018 | 98.7 | - | - | PCA-based feature selection [11] |
| LSTM-FF (Hybrid) | CIC-DoS2017 | 99.7 | 99.5 | 97.5 | For Low-Rate DoS attacks, low FAR of 0.03% [12] |
| Weighted Ensemble (CNN, BiLSTM, RF, LR) | BOT-IOT | 100.0 | - | - | Integrated via soft-voting [10] |
| Weighted Ensemble (CNN, BiLSTM, RF, LR) | CICIOT2023 | 99.2 | - | - | Integrated via soft-voting [10] |
| RNN | CIC-DDoS2019 | 97.9 | - | - | With adaptive temporal windows [13] |
Deep learning models, particularly hybrids like LSTM-FF and ensembles, achieve top-tier accuracy in detecting sophisticated attacks like Low-Rate DoS [12]. Traditional machine learning models, especially Random Forest, remain highly competitive, often offering a superior balance of high accuracy and computational efficiency [11] [14].
Performance in Drug Response Prediction
Table 2: Cross-dataset generalization performance of Drug Response Prediction (DRP) models.
| Source Dataset | Target Dataset | Generalization Performance | Key Insight |
|---|---|---|---|
| CCLE, gCSI, GDSCv1, GDSCv2 | Various | Substantial performance drop on unseen datasets | Highlights the importance of cross-dataset benchmarks [9] |
| CTRPv2 | Various | Highest generalization scores across target datasets | Most effective source dataset for training robust DRP models [9] |
| Random Forest / XGBoost | IEC 60870-5-104 / SDN | F1-Score: 93.57% / 99.97% | Often outperform deeper learning models despite simpler architecture [14] |
Benchmarking in DRP reveals that no single model consistently outperforms all others across every dataset. The source of the training data (e.g., CTRPv2) can be as critical to generalization performance as the model architecture itself [9].
Table 3: Key resources and datasets for benchmarking computational models.
| Resource Name | Type | Primary Function | Field of Application |
|---|---|---|---|
| CIC-DDoS2019 | Dataset | Provides labeled benign and sophisticated DDoS attack traffic for training and evaluating IDS models. | Network Security / IDS |
| BOT-IOT, CICIOT2023, IOT23 | Dataset | A set of benchmark datasets used to compare IoT attack detection models under diverse network scenarios. | IoT Security |
| CCLE, CTRPv2, gCSI, GDSC | Dataset | A collection of drug screening studies containing cell line viability data (AUC) in response to compound treatments. | Drug Discovery / DRP |
| SMOTE | Algorithm | Synthetically generates samples for the minority class to mitigate model bias caused by class imbalance. | Data Preprocessing |
| Quantile Uniform Transformation | Algorithm | Reduces skewness in feature distributions while preserving critical information like attack signatures. | Data Preprocessing |
| Principal Component Analysis (PCA) | Algorithm | Reduces the dimensionality of data, improving computational efficiency and sometimes model performance. | Feature Selection |
| IMPROVE Framework | Software | A standardized Python package and benchmarking framework for reproducible drug response prediction. | Drug Discovery / DRP |
| GPMin / GOFEE | Software | ML-assisted algorithms for accelerating local and global geometry optimization of surface and interface structures. | Computational Materials Science |
Workflow and Relationship Visualizations
Diagram 1: Generalized workflow for benchmarking computational methods, covering data preparation, model training, evaluation, and applicability domain definition.
Diagram 2: Core methods for defining the Applicability Domain (AD), showing the distinct approaches of novelty detection and confidence estimation.
The Role of Standardized Datasets and Benchmarking Frameworks
In computational sciences, particularly in data-intensive fields like drug discovery and cybersecurity, standardized datasets and benchmarking frameworks provide the foundational infrastructure for objective performance evaluation. These resources allow researchers to compare novel algorithms and computational methods against established baselines under consistent conditions, enabling accurate assessment of progress and practical utility [15]. A benchmarking dataset is formally defined as any resource explicitly published for evaluation purposes, publicly available or accessible upon request, and accompanied by clear evaluation methodologies [15]. This distinguishes them from general datasets used for unsupervised pre-training or novel dataset creation.
The critical importance of these tools stems from their role in mitigating experimental variability and ensuring reproducible findings. As computational approaches become increasingly integrated into high-stakes domains like pharmaceutical development, where experimental validation remains extraordinarily costly and time-consuming, robust benchmarking practices help prioritize the most promising candidates for further investigation [16] [17]. Furthermore, in cybersecurity applications such as intrusion detection systems for Internet of Things (IoT) environments, benchmarking enables researchers to evaluate both detection accuracy and computational efficiency—essential considerations for resource-constrained environments [3] [18].
Characteristics of Effective Benchmarking Datasets
Essential Qualities and Design Principles
Effective benchmarking datasets share several defining characteristics that ensure their utility and longevity within research communities. According to computational science literature, high-quality benchmarks should be:
- Standardized and validated collections specifically designed for evaluation purposes [15]
- Representative of real-world conditions to provide realistic assessment environments [15]
- Periodically updated to reflect evolving challenges and new threat vectors [15]
- Structured for scalability through category spaces and hierarchies that allow augmentation with additional samples and categories [15]
- Accompanied by clear evaluation metrics and methodologies to ensure consistent application [15]
The principle of diversity, richness, and scalability (DiRS) is particularly emphasized in domains like remote sensing and GeoAI, where benchmarks must demonstrate high within-class diversity, between-class similarity, and multiple semantic categories to support generalization and discrimination of fine-grained content [15].
Domain-Specific Benchmarking Examples
Table 1: Notable Benchmarking Datasets Across Computational Domains
| Domain | Dataset Name | Application Focus | Key Characteristics |
|---|---|---|---|
| IoT Security | CICIoT2023 [3] | DoS, DDoS, and Mirai attack classification | Comprehensive attack variants, realistic network traffic patterns |
| Medical Imaging | Abdomen-1K [15] | Computed tomography analysis | 1,112 CT scans with enhanced variety and diversity |
| Medical Imaging | Medical Segmentation Decathlon [15] | Multi-organ segmentation | 10 different segmentation challenges across various modalities |
| Code Migration | MigrationBench [19] | Java repository migration | 5,102 open-source Java 8 Maven repositories with test validation |
| Code Migration | Poly-MigrationBench [19] | Multi-language migration | .NET, Node.js, and Python repositories for cross-platform migration |
| Natural Language Processing | GLUE [15] | General language understanding | Diverse tasks extracted from news, social media, books, and Wikipedia |
Benchmarking Methodologies and Evaluation Metrics
Components of a Benchmarking Framework
A comprehensive machine learning benchmark typically consists of four core components: (1) a dataset providing standardized inputs; (2) an objective defining the task to be performed; (3) metrics to quantify progress toward objectives; and (4) reporting protocols to ensure consistent communication of results [15]. These components work synergistically to create environments where algorithmic performance can be objectively quantified and compared.
Frameworks like the Language Model Evaluation Harness from EleutherAI provide unified infrastructure to benchmark machine learning models on large numbers of evaluation tasks, structuring diverse datasets, configurations, and evaluation strategies in one place [20]. Similarly, Stanford's HELM (Holistic Evaluation of Language Models) takes a comprehensive approach by prioritizing scenarios and metrics based on societal relevance, coverage across languages, and computational feasibility [20].
Key Evaluation Metrics
Table 2: Common Evaluation Metrics in Computational Benchmarking
| Metric | Calculation | Interpretation | Optimal Use Cases |
|---|---|---|---|
| Accuracy | (TP+TN)/(TP+TN+FP+FN) | Overall correctness | Balanced class distributions |
| Precision | TP/(TP+FP) | Proportion of true positives among positive predictions | When false positives are costly |
| Recall (Sensitivity) | TP/(TP+FN) | Proportion of actual positives correctly identified | When false negatives are costly |
| F1-Score | 2×(Precision×Recall)/(Precision+Recall) | Harmonic mean of precision and recall | Imbalanced datasets |
| AUC-ROC | Area under ROC curve | Overall performance across classification thresholds | Comprehensive model assessment |
While accuracy remains commonly reported, it may be the least informative metric in scenarios with class imbalance, such as manufacturing datasets or cybersecurity threat detection [15]. In these contexts, precision, recall, and F1-score offer more nuanced insights into algorithm performance. For example, in IoT security research, the F1-score provides a balanced assessment of model capability in distinguishing between attack types and normal traffic [3].
Experimental Protocols in Computational Research
IoT Security Assessment Protocol
Research evaluating machine learning approaches for attack classification in IoT networks demonstrates a comprehensive benchmarking methodology [3]. The experimental protocol encompasses:
- Data Preprocessing: Addressing class imbalance through undersampling techniques to improve model reliability and generalizability [3]
- Feature Selection: Implementing multiple selection methods including Chi-square, Principal Component Analysis (PCA), and Random Forest Regressor to identify optimal feature subsets [3]
- Model Training: Applying five supervised machine learning algorithms (Random Forest, Gradient Boosting, Naive Bayes, Decision Tree, and K-Nearest Neighbors) under consistent conditions [3]
- Performance Evaluation: Measuring accuracy, precision, sensitivity, and F1-score metrics alongside computational efficiency indicators like training and prediction times [3]
This methodology revealed that the Random Forest Regressor feature selection method combined with Decision Tree classification achieved state-of-the-art performance (99.99% accuracy) while significantly improving computational efficiency—reducing training time by 98.71% and prediction time by 99.53% compared to previous studies [3].
IoT Security Benchmarking Workflow
Drug Discovery Evaluation Protocol
In computational drug discovery, benchmarking follows rigorous protocols to assess predictive accuracy for key physicochemical and absorption, distribution, metabolism, and excretion (ADME) properties [21]. Standard methodologies include:
- Experimental Data Curation: Compiling large, high-quality datasets from published studies and proprietary sources, acknowledging challenges related to experimental error and data volume [21]
- Method Comparison: Evaluating diverse computational approaches ranging from quantum mechanics calculations to machine learning models against standardized datasets [17] [22]
- Statistical Validation: Employing multiple error metrics including mean signed error (MSE), mean unsigned error (MUE), and maximum error (MAXE) to comprehensively quantify performance [22]
For proton affinity predictions, benchmarking studies systematically evaluate density functional theory (DFT) functionals (B3LYP, BP86, PBEPBE, APFD, wB97XD, M062X) using the flexible def2tzvp basis set, comparing calculated values against experimental reference data from the NIST database [22]. These protocols identified the M062X functional as providing optimal accuracy for predicting proton affinities and gas-phase basicities across diverse molecular structures [22].
Drug Discovery Benchmarking Workflow
Table 3: Essential Computational Tools for Benchmarking Studies
| Tool Category | Specific Tools | Primary Function | Application Context |
|---|---|---|---|
| Quantum Chemistry Software | Gaussian09 [22] | Thermochemistry calculations | Proton affinity predictions, molecular property computation |
| Evaluation Frameworks | Language Model Evaluation Harness [20] | Unified benchmarking framework | Evaluating generative capabilities and reasoning tasks |
| Evaluation Frameworks | Stanford HELM [20] | Holistic language model evaluation | Multi-metric assessment across diverse scenarios |
| Evaluation Frameworks | PromptBench [20] | Prompt engineering evaluation | Benchmarking prompt-level adversarial attacks |
| Evaluation Frameworks | DeepEval [20] | LLM evaluation platform | Regression testing and model evaluation on cloud |
| Dataset Repositories | Hugging Face [19] | Dataset hosting and sharing | Access to MigrationBench and Poly-MigrationBench |
| Dataset Repositories | GitHub [19] | Code and dataset distribution | Open-source benchmarking implementations |
Benchmarking Datasets as Research Reagents
In computational research, benchmarking datasets themselves function as essential research reagents, providing standardized substrates for method validation:
- CICIoT2023: Serves as a validated benchmark for IoT security research, containing diverse attack variants including Denial of Service (DoS), Distributed Denial of Service (DDoS), and Mirai attacks [3]
- MigrationBench: Provides 5,102 open-source Java 8 Maven repositories for evaluating code migration tools, with quality filters ensuring inclusion of projects with sufficient complexity and test coverage [19]
- Medical Segmentation Decathlon: Offers 10 different segmentation challenges across various imaging modalities and anatomical structures, testing algorithm robustness across diverse medical imaging tasks [15]
Challenges and Future Directions in Benchmarking
Despite their critical importance, benchmarking datasets and frameworks face several persistent challenges that limit their effectiveness and adoption. A significant issue across multiple domains is the limited availability of specialized public datasets. In manufacturing and cyber-physical systems, for example, the scarcity of tailored benchmarking datasets restricts standardized evaluation and fair algorithm comparison [15]. Similarly, medical imaging research suffers from insufficient large, representative labeled datasets due to privacy concerns, cost constraints, and data fragmentation across institutions [15].
Community-wide overfitting presents another fundamental challenge, particularly in computer vision and medical imaging, where researchers repeatedly optimize algorithms on the same public benchmarks, potentially inflating performance metrics without corresponding real-world improvements [15]. To mitigate this, evaluation on multiple public and private datasets is recommended, though this only partially addresses the underlying bias [15].
Future directions in benchmarking emphasize several promising approaches:
- Federated learning frameworks that enable secure access to sensitive data without compromising privacy, particularly valuable for healthcare applications [15]
- Dynamic benchmark development that evolves with changing requirements and emerging challenges, as exemplified by the DiRS principle in remote sensing [15]
- Multi-dimensional evaluation that moves beyond narrow accuracy metrics to assess computational efficiency, robustness, fairness, and practical deployability [3] [15]
- Cross-platform benchmarking that enables performance comparison across diverse computational environments and resource constraints [19]
As computational methods continue to advance, the role of standardized datasets and benchmarking frameworks will only grow in importance, providing the critical infrastructure needed to distinguish incremental optimization from genuine scientific progress across research domains.
Within computational methods research, particularly in fields requiring high-fidelity simulations like drug development, Multidisciplinary Design Optimization (MDO) faces a fundamental challenge: balancing model accuracy with computational cost. Multifidelity methods address this by strategically combining information sources of varying fidelity—from fast, approximate models to slow, high-accuracy simulations—to enable efficient and scalable design exploration [23]. The core challenge lies in selecting appropriate fidelity levels and coupling them effectively. Without rigorous benchmarking, comparing the performance of these numerous multifidelity methods remains difficult, hindering the adoption of robust optimization strategies in scientific and industrial applications. This guide provides a structured framework for assessing these methods, enabling researchers to make informed decisions when deploying multifidelity optimization for complex problems like drug design and molecular simulation.
A Standardized Benchmarking Framework
A comprehensive benchmarking framework is essential for the objective comparison of multifidelity optimization methods. According to community standards, test problems are classified into three levels [23]:
- L1 Problems: Computationally cheap analytical functions with known exact solutions, ideal for rapid prototyping and controlled algorithmic assessment.
- L2 Problems: Simplified engineering applications executable with reduced computational expense.
- L3 Problems: Complex engineering use cases, often involving multi-physics couplings.
This guide focuses on L1 analytical benchmarks, which provide a controlled environment for stress-testing algorithms. Their closed-form nature ensures high reproducibility, computational efficiency, and isolates algorithmic behavior from numerical artifacts [23]. The global optima of these benchmarks are known by construction, allowing for precise quantification of optimization performance.
Core Analytical Benchmark Problems
The following suite of L1 benchmark problems is designed to capture mathematical challenges endemic to real-world computational tasks, including high dimensionality, multimodality, discontinuities, and noise [23].
Table 1: Suite of Analytical Benchmark Problems for Multifidelity Optimization
| Benchmark Problem | Key Mathematical Characteristics | Relevance to Real-World Applications |
|---|---|---|
| Forrester Function (Continuous & Discontinuous) | Non-linear, one-dimensional, strong non-linearity | Tests ability to model non-linear relationships between model fidelities. |
| Rosenbrock Function | Continuous, non-convex, curved parabolic valley | Represents problems with long, flat optimal regions and sharp gradients. |
| Rastrigin Function (Shifted & Rotated) | Highly multimodal, separable, scalable dimensionality | Mimics landscapes with many local optima, testing escape from suboptimal solutions. |
| Heterogeneous Function | Mixed properties (e.g., linear, quadratic, sinusoidal regions) | Challenges methods to adapt to varying local function behaviors. |
| Coupled Spring-Mass System | Physics-based, coupled interactions | Represents simple dynamical systems with interacting components. |
| Pacioreck Function with Noise | Affected by artificial noise | Tests robustness to uncertainties in function evaluations. |
Defining Fidelity and Discrepancy
In a multifidelity setting, the function to be minimized is the highest-fidelity function, ( f1(\mathbf{x}) ). The optimization leverages a spectrum of ( L ) cheaper-to-evaluate approximations, from ( f1(\mathbf{x}) ) down to ( f_L(\mathbf{x}) ), the lowest-fidelity level available [23]. A critical aspect of these benchmarks is the discrepancy type, which describes the relationship between different fidelities. A linear discrepancy is simpler to model than a non-linear one, and the selected benchmarks allow for assessing how well methods can handle these relationships as the number of available fidelities changes [23].
Quantitative Assessment and Performance Metrics
A rigorous assessment requires predefined metrics to quantify performance over measurable objectives. The proposed metrics evaluate both optimization effectiveness and global approximation accuracy [23].
Table 2: Performance Metrics for Multifidelity Optimization Assessment
| Metric Category | Specific Metric | Definition and Purpose |
|---|---|---|
| Optimization Effectiveness | Convergence Speed | Number of high-fidelity evaluations or total computational cost required to find the optimum. |
| Solution Accuracy | Difference between the found optimum ( f(\mathbf{x}^*) ) and the known global optimum ( f^\star ). | |
| Robustness | Consistency of performance across multiple runs with different initial samples. | |
| Global Approximation Accuracy | Mean Squared Error (MSE) | Average squared difference between the surrogate model and the high-fidelity function across the design space. |
| Coefficient of Determination (( R^2 )) | Proportion of variance in the high-fidelity model explained by the multifidelity surrogate. |
Experimental Protocol for Method Comparison
To ensure a fair and meaningful comparison between different multifidelity optimization methods, the following experimental protocol is recommended.
Experimental Workflow
The diagram below outlines the logical workflow for a standardized benchmarking experiment.
Recommended Experimental Setup
For reproducible results, researchers should adhere to the following setup for the benchmark problems [23]:
- Initial Sampling: Use a space-filling design, such as Latin Hypercube Sampling (LHS), to generate an initial set of sample points for the lowest-fidelity model. The sample size should be a multiple of the problem's dimensionality.
- Infill Strategy: Define a consistent acquisition function (e.g., Expected Improvement, Lower Confidence Bound) for selecting new evaluation points based on the multifidelity surrogate model.
- Termination Criteria: Standardize stopping conditions, such as a maximum number of high-fidelity evaluations, a tolerance in solution improvement between iterations, or a computational budget.
- Repetitions: Perform multiple independent runs of each optimization method from different initial samples to account for stochasticity and compute robust performance statistics.
The Scientist's Toolkit for Multifidelity Optimization
Implementing and testing multifidelity optimization methods requires a specific set of computational tools and resources.
Table 3: Essential Research Reagent Solutions for Multifidelity Benchmarking
| Item | Function in the Benchmarking Process |
|---|---|
| L1 Benchmark Code Suite | Pre-implemented analytical benchmark functions in languages like Python, MATLAB, or Fortran. Provides a standardized, ready-to-use testbed. [23] |
| Multifidelity Optimization Software | Frameworks such as mf2 or Dakota that provide built-in algorithms for multifidelity surrogate modeling (e.g., Co-Kriging) and optimization. |
| Performance Metric Calculators | Scripts to compute standardized metrics (see Table 2) from optimization history data, ensuring consistent evaluation across studies. |
| Color Contrast Checker | A tool like the WebAIM Color Contrast Checker to ensure all visualizations (e.g., convergence plots, surrogate models) meet accessibility standards (WCAG AA). [24] |
The systematic assessment of multifidelity optimization methods through standardized analytical benchmarks is a critical step toward their reliable application in computationally intensive fields like drug development. The framework presented here—encompassing a diverse suite of benchmark problems, quantitative performance metrics, and a detailed experimental protocol—provides researchers with the necessary tools for objective comparison.
Based on this benchmarking approach, the primary lessons are:
- No Single Best Method: The performance of a multifidelity method is highly dependent on the mathematical characteristics of the problem, such as modality and fidelity discrepancy.
- Controlled Testing is Crucial: L1 benchmarks are indispensable for understanding fundamental algorithmic behaviors before progressing to more expensive L2 or L3 engineering problems.
- Rigorous Protocol Ensures Fairness: Adherence to a standardized experimental setup, including initial sampling, termination criteria, and multiple runs, is fundamental for producing credible and comparable results.
This benchmarking framework equips scientists and engineers to select and tailor multifidelity optimization strategies that can significantly accelerate the discovery and development pipeline by making the most efficient use of computational resources across model fidelity levels.
A Landscape of Computational Tools: From QSAR and Docking to AI and Quantum Mechanics
The predictive assessment of physicochemical properties and toxicokinetic profiles is a critical step in the development of new chemical entities, particularly in the pharmaceutical and regulatory sectors. Quantitative Structure-Activity Relationship (QSAR) tools have emerged as indispensable computational methods for filling data gaps by estimating properties based on molecular structure, thereby reducing reliance on costly and time-consuming experimental testing. These tools operate on the fundamental principle that similar molecular structures exhibit similar biological activities and properties, a concept formally known as the similarity-property principle [25] [26]. The evolution of QSAR methodologies from simple linear regression models utilizing few physicochemical parameters to complex machine learning algorithms capable of processing thousands of chemical descriptors has significantly expanded their predictive capabilities and application domains [25].
The reliability of QSAR predictions is of paramount importance for regulatory acceptance and safety assessment. Consequently, benchmarking the predictive accuracy and applicability domains of these tools has become a central focus in computational toxicology and drug design research. This review objectively compares the performance of prominent QSAR tools, with particular emphasis on the OECD QSAR Toolbox, and examines the experimental protocols and benchmarking methodologies essential for validating their predictive capabilities for physicochemical and toxicokinetic properties.
The OECD QSAR Toolbox
The OECD QSAR Toolbox represents a comprehensive software solution developed through international collaboration to promote the regulatory acceptance of (Q)SAR methodologies [27] [28]. As a freely available application, it supports transparent chemical hazard assessment by providing functionalities for experimental data retrieval, metabolism simulation, and chemical property profiling. The Toolbox incorporates 62 databases covering approximately 155,000 chemicals and containing over 3.3 million experimental data points, making it one of the most extensive resources for chemical safety assessment [27].
The seminal workflow of the Toolbox involves: (1) identifying relevant structural characteristics and potential mechanisms or modes of action of a target chemical; (2) identifying other chemicals that share the same structural characteristics and/or mechanisms; and (3) using existing experimental data from these analogous chemicals to fill data gaps through read-across or trend analysis [28]. The system also incorporates various external QSAR models that can be executed to generate supporting evidence for chemical assessments [27].
Other QSAR Platforms and Frameworks
While the OECD QSAR Toolbox represents a major integrative effort, several other platforms and methodologies contribute to the QSAR landscape. OrbiTox, developed by Sciome, offers chemistry-based similarity searching, molecular descriptors, over a million data points, more than 100 QSAR models, and a built-in metabolism predictor [29]. Similarly, research continues to develop novel QSAR approaches such as Topological Regression (TR), which provides a statistically grounded, computationally fast, and interpretable technique for predicting drug responses while addressing the challenge of activity cliffs—pairs of structurally similar compounds with large differences in potency [30].
The development of robust QSAR models relies on specialized software packages for molecular descriptor calculation, including PaDEL, Mordred, and RDKit [30]. Deep-learning methods such as Chemprop utilize directed message-passing neural networks to learn molecular representations directly from graphs for property prediction, demonstrating particular utility in antibiotic discovery and lipophilicity prediction [30].
Table 1: Comparison of Major QSAR Platforms and Their Capabilities
| Platform | Primary Focus | Data Resources | Key Functionalities | Regulatory Acceptance |
|---|---|---|---|---|
| OECD QSAR Toolbox | Integrated chemical hazard assessment | 62 databases, 155K+ chemicals, 3.3M+ data points [27] | Profiling, read-across, metabolic simulator, QSAR model integration | High (OECD-developed) |
| OrbiTox (Sciome) | Read-across and QSAR modeling | 1M+ data points, 100+ QSAR models [29] | Chemistry-based similarity searching, metabolism prediction | Growing (Regulatory submissions focus) |
| Topological Regression | Drug response prediction | Dependent on input datasets [30] | Interpretable similarity-based regression, activity cliff handling | Research phase |
| Chemprop | Property prediction from molecular graphs | Dependent on input datasets [30] | Message-passing neural networks, embedded feature extraction | Research phase |
Experimental Protocols for QSAR Tool Benchmarking
Standardized Workflow for Predictive Assessment
The evaluation of QSAR tool performance requires carefully designed experimental protocols that ensure reproducibility and statistical significance. A robust benchmarking methodology typically follows these essential steps:
Dataset Curation and Preprocessing: High-quality datasets with well-characterized chemical structures and reliably measured experimental values for physicochemical and toxicokinetic properties form the foundation of any benchmarking study. The chemical diversity and structural complexity of the compounds in the dataset must adequately represent the application domain of interest [25]. Data preprocessing steps may include normalization, handling of missing values, and removal of duplicates.
Chemical Representation and Descriptor Calculation: Molecular structures are converted into machine-readable mathematical representations using various descriptor types. These may include classical molecular descriptors encoding specific computed or measured attributes, molecular fingerprints such as Extended-Connectivity Fingerprints (ECFPs) that encode chemical substructures, or graph representations that characterize 2D chemical structures as graphs with atoms as vertices and bonds as edges [30].
Chemical Category Formation: For read-across approaches, chemicals are grouped into toxicologically meaningful categories based on structural similarity, mechanistic similarity, or shared metabolic pathways [27]. The OECD QSAR Toolbox provides several profiling schemes (profilers) to identify the affiliation of target chemicals with predefined categories containing functional groups or alerts associated with specific mechanisms of action [27].
Model Application and Prediction: The curated dataset is processed through the QSAR tools being evaluated to generate predictions for the target properties. This may involve read-across from similar compounds with experimental data, application of QSAR models, or trend analysis within chemical categories [27].
Performance Validation and Statistical Analysis: Predictive performance is quantified by comparing tool predictions with held-out experimental data using statistical metrics. Common measures include accuracy, precision, sensitivity, and F1-score for classification endpoints, and correlation coefficients, root mean square error (RMSE), and mean absolute error (MAE) for continuous endpoints [3]. Cross-validation techniques are employed to ensure robust performance estimation [25].
The following diagram illustrates the generalized workflow for benchmarking QSAR tools:
Addressing Methodological Challenges
Robust benchmarking must account for several methodological challenges inherent to QSAR modeling. The applicability domain of each tool must be carefully considered to avoid extrapolation beyond the chemical space for which the tool was designed [25]. The presence of activity cliffs, where small structural modifications result in significant activity changes, can substantially impact predictive performance and requires specific handling strategies [30].
Class imbalance in datasets represents another critical challenge, as unequal representation of different activity classes can bias model performance. Techniques such as undersampling have been successfully employed to address this issue in computational toxicology studies [3]. Furthermore, feature selection methods including Chi-square tests, Principal Component Analysis (PCA), and Random Forest Regressor (RFR) can enhance model performance and computational efficiency by identifying the most relevant molecular descriptors [3].
Essential Research Reagent Solutions
The effective application of QSAR tools requires a suite of computational "research reagents" that facilitate various stages of the predictive workflow. These foundational resources enable everything from initial chemical representation to final model interpretation.
Table 2: Essential Research Reagent Solutions for QSAR Studies
| Research Reagent | Category | Primary Function | Examples/Implementations |
|---|---|---|---|
| Molecular Descriptors | Chemical Representation | Quantify structural and physicochemical features | PaDEL, Mordred, RDKit [30] |
| Molecular Fingerprints | Chemical Representation | Encode substructural patterns as bit strings | Extended-Connectivity Fingerprints (ECFPs) [30] |
| Profiling Schemes | Category Formation | Identify structural alerts and mechanism-based groups | OECD QSAR Toolbox Profilers [27] |
| Metabolic Simulators | Transformation Prediction | Predict biotic and abiotic transformation products | Built-in metabolism simulators [27] |
| Similarity Metrics | Read-Across | Quantify structural similarity between compounds | Tanimoto coefficient, Euclidean distance [30] |
| Feature Selection Methods | Model Optimization | Identify most relevant descriptors | Chi-square, PCA, Random Forest Regressor [3] |
Molecular descriptors and fingerprints serve as the fundamental language for representing chemical structures in machine-readable formats, enabling quantitative comparisons between compounds [30]. Profiling schemes, such as those implemented in the OECD QSAR Toolbox, facilitate the identification of structurally and mechanistically related compounds, forming the basis for read-across and category formation [27]. Metabolic simulators predict potential transformation products, which is crucial for toxicokinetic assessments as metabolites may exhibit different properties and activities compared to parent compounds [27].
Similarity metrics provide quantitative measures of structural resemblance, guiding the identification of suitable source compounds for read-across predictions [30]. Finally, feature selection methods enhance model interpretability and computational efficiency by identifying the most relevant molecular descriptors for specific predictive tasks [3].
Performance Benchmarking and Comparison
Quantitative Performance Assessment
Rigorous benchmarking studies provide valuable insights into the relative performance of different QSAR approaches. While direct comparative studies between the OECD QSAR Toolbox and alternative platforms are limited in the available literature, performance data from individual studies illustrate the capabilities of contemporary QSAR methodologies.
In the evaluation of QSAR models for biological activity prediction, topological regression (TR) has demonstrated comparable or superior performance to deep-learning-based QSAR models across 530 ChEMBL human target activity datasets, while offering enhanced interpretability through the extraction of approximate isometry between chemical space and activity space [30]. Similarly, in specialized applications such as IoT security (which employs similar classification challenges), machine learning approaches including Random Forest, Decision Tree, and Gradient Boosting have achieved accuracies of 99.99% with appropriate feature selection methods, demonstrating the potential performance of well-optimized predictive models [3].
The OECD QSAR Toolbox has demonstrated practical utility across diverse regulatory and industry applications. Case studies document its use in evaluating biocides under Regulation (EC) No 528/2012, assessing agrochemicals, supporting REACH regulatory submissions, and conducting preliminary screening of raw materials for cosmetics [27]. These real-world applications provide evidence of the Toolbox's predictive capabilities, though quantitative performance metrics for specific physicochemical and toxicokinetic properties are not uniformly reported in the available literature.
Computational Efficiency Considerations
Beyond predictive accuracy, computational efficiency represents a critical practical consideration, particularly for large-scale chemical assessments. Recent advances have demonstrated significant improvements in training and prediction times without compromising accuracy. For instance, optimized Decision Tree models have achieved a 98.71% reduction in training time and a 99.53% reduction in prediction time compared to previously reported results while maintaining superior accuracy [3]. Although these results come from a different application domain, they highlight the importance of computational efficiency in practical implementations of predictive algorithms.
Feature selection methods substantially impact computational efficiency. Studies comparing Chi-square, PCA, and Random Forest Regressor (RFR) feature selection techniques have found that RFR consistently outperforms other methods, contributing to both enhanced accuracy and reduced computational requirements [3]. The OECD QSAR Toolbox addresses efficiency challenges through its streamlined workflow, which incorporates theoretical knowledge, experimental data, and computational tools organized in a logical sequence to simplify the application of non-test methods [27].
The following diagram illustrates the relationship between key factors influencing QSAR tool performance:
Emerging Trends and Development Needs
The field of QSAR modeling continues to evolve, with several emerging trends shaping its future development. The integration of deep learning methodologies represents a significant advancement, offering enhanced capabilities for learning complex functional relationships between molecular descriptors and activity [25]. However, these approaches often face challenges in interpretability, prompting research into explainable AI techniques for molecular design [30].
The development of universal QSAR models capable of reliably predicting the properties of diverse chemical structures remains an aspirational goal. Achieving this objective requires addressing several fundamental challenges: (1) assembling sufficient structure-activity relationship instances to cope with the complexity and diversity of molecular structures and action mechanisms; (2) developing precise molecular descriptors that balance dimensionality with computational cost; and (3) implementing powerful and flexible mathematical models to learn complex structure-activity relationships [25].
Bibliometric analyses of QSAR publications reveal evolutionary trends in the field, including increases in dataset sizes, diversification of descriptor types, and growing adoption of advanced machine learning algorithms [25]. These trends reflect ongoing efforts to expand the applicability domains of QSAR models and enhance their predictive performance across broader chemical spaces.
This review has examined the current landscape of QSAR tools for predicting physicochemical and toxicokinetic properties, with particular focus on the OECD QSAR Toolbox as a comprehensive, regulatory-supported platform. The benchmarking of these tools requires carefully designed experimental protocols that address dataset curation, chemical representation, category formation, model application, and performance validation.
The OECD QSAR Toolbox distinguishes itself through its extensive data resources, integrative workflow combining multiple assessment approaches, and widespread adoption in regulatory contexts. While emerging approaches such as topological regression and deep learning-based models show promise for enhanced performance and interpretability, the Toolbox remains a cornerstone in computational toxicology due to its transparency, comprehensive functionality, and regulatory acceptance.
As the field advances, the convergence of larger and higher-quality datasets, more accurate molecular descriptors, and sophisticated modeling techniques will continue to improve the predictive ability, interpretability, and application domains of QSAR tools. These developments will further solidify the role of computational approaches in chemical safety assessment and drug discovery, providing efficient and effective means for predicting essential physicochemical and toxicokinetic properties.
Molecular docking is a cornerstone of computational drug discovery, enabling the prediction of how small molecules interact with biological targets. The accuracy of these predictions hinges on the docking protocols and scoring functions used to approximate binding affinity. However, with a plethora of available tools and functions, their performance can vary significantly based on the target and scenario. This creates an critical need for rigorous benchmarking—the systematic comparison of computational methods using standardized datasets and metrics—to provide actionable insights for researchers and drive method development forward. This guide objectively compares the performance of current docking and scoring methodologies, framing the findings within the broader thesis that robust benchmarking is fundamental for ensuring the accuracy and reliability of computational methods in structural biology and drug design.
Performance Comparison of Docking and Scoring Methods
The performance of docking tools and scoring functions is highly context-dependent, influenced by the protein target, the presence of resistance mutations, and the chemical space of the screened ligands. The following tables summarize key quantitative findings from recent benchmarking studies.
Table 1: Benchmarking Docking Tools and ML Rescoring against PfDHFR Variants [31]
| Target Variant | Docking Tool | Rescoring Method | Primary Metric (EF 1%) | Performance Summary |
|---|---|---|---|---|
| Wild-Type (WT) PfDHFR | AutoDock Vina | None (Default Scoring) | Worse-than-random | Poor initial screening performance |
| Wild-Type (WT) PfDHFR | AutoDock Vina | RF-Score-VS v2 | Better-than-random | Significant improvement with ML rescoring |
| Wild-Type (WT) PfDHFR | AutoDock Vina | CNN-Score | Better-than-random | Significant improvement with ML rescoring |
| Wild-Type (WT) PfDHFR | PLANTS | CNN-Score | 28 | Best overall enrichment for WT variant |
| Quadruple-Mutant (Q) PfDHFR | FRED | CNN-Score | 31 | Best overall enrichment for resistant Q variant |
EF 1%: Enrichment Factor at the top 1% of the screened library; a higher value indicates better ability to prioritize active compounds.
Table 2: Pairwise Performance Comparison of MOE Scoring Functions [32]
| Scoring Function | Type | Best Docking Score (BestDS) | Best RMSD (BestRMSD) | RMSD of BestDS Pose (RMSD_BestDS) | DS of BestRMSD Pose (DS_BestRMSD) |
|---|---|---|---|---|---|
| Alpha HB | Empirical | Moderate | High Performance | Moderate | Moderate |
| London dG | Empirical | Moderate | High Performance | Moderate | Moderate |
| ASE | Empirical | Moderate | Moderate | Moderate | Moderate |
| Affinity dG | Empirical | Moderate | Moderate | Moderate | Moderate |
| GBVI/WSA dG | Force-Field | Moderate | Moderate | Moderate | Moderate |
Performance assessed on the CASF-2013 benchmark (195 complexes). The BestRMSD output, which measures pose prediction accuracy, was the most informative for distinguishing between scoring functions, with Alpha HB and London dG showing the highest comparability and performance [32].
Table 3: Impact of Training Data on ML Score Prediction (Chemprop) [33]
| Training Set Size | Sampling Strategy | Overall Pearson (AmpC) | logAUC (Top 0.01%) | Key Insight |
|---|---|---|---|---|
| 1,000 | Random | 0.65 | 0.49 (est.) | Low correlation, poor enrichment of top scorers |
| 100,000 | Random | 0.83 | 0.49 | High correlation does not guarantee good enrichment |
| 100,000 | Stratified | 0.76 | 0.77 | Strategic sampling significantly improves enrichment |
Experimental Protocols for Key Benchmarking Studies
Benchmarking Protocol for Antimalarial Target (PfDHFR)
A comprehensive benchmark was conducted to evaluate screening performance against both wild-type and drug-resistant Plasmodium falciparum dihydrofolate reductase (PfDHFR) [31].
- Protein Preparation: Crystal structures for WT (PDB: 6A2M) and quadruple-mutant (Q) PfDHFR (PDB: 6KP2) were obtained from the Protein Data Bank. Proteins were prepared using OpenEye's "Make Receptor" GUI: removing water molecules, ions, and redundant chains; adding and optimizing hydrogen atoms [31].
- Benchmark Set Preparation: The DEKOIS 2.0 protocol was employed to create benchmark sets for each variant. Each set contained 40 known bioactive molecules and 1,200 structurally similar but presumed inactive decoys (a 1:30 ratio). Ligands were prepared with Omega to generate multiple conformations [31].
- Docking Experiments: Three docking tools were evaluated:
- AutoDock Vina: Receptor and ligands converted to PDBQT format. Grid boxes were centered on the binding site.
- FRED: Required pre-generated ligand conformations.
- PLANTS: Utilized SPORES for correct atom typing.
- Machine Learning Rescoring: The top poses from each docking tool were rescored using two pretrained ML scoring functions: RF-Score-VS v2 (Random Forest-based) and CNN-Score (Convolutional Neural Network-based).
- Performance Evaluation: Screening quality was assessed using:
- Enrichment Factor at 1% (EF 1%): Measures the concentration of true actives in the top 1% of the ranked list.
- pROC-AUC: Area under the semi-log ROC curve, assessing early enrichment.
- pROC-Chemotype Plots: Evaluate the retrieval of diverse, high-affinity chemotypes.
Community Standard Benchmarking Guidelines
Essential guidelines for rigorous computational benchmarking, distilled from community best practices, include [34]:
- Define Purpose and Scope: Clearly state whether the benchmark is a "neutral" comparison or for demonstrating a new method's advantage. The selection of methods and datasets should flow from this purpose.
- Comprehensive Method Selection: Neutral benchmarks should strive to include all available methods, or at least a representative subset, with clear and unbiased inclusion criteria (e.g., software availability, usability).
- Use of Diverse Datasets: Incorporate a variety of benchmark datasets, including both simulated data (with known ground truth) and real experimental data. Datasets should reflect relevant biological and chemical challenges.
- Avoid Bias: Apply the same level of optimization and trouble-shooting to all methods being compared. Do not over-tune a new method while using out-of-the-box settings for competitors.
- Employ Robust Metrics: Use multiple, complementary performance metrics (e.g., EF, AUC, RMSD) to provide a holistic view of method performance and trade-offs.
Workflow and Relationship Diagrams
The following diagram illustrates the standard workflow for a structure-based virtual screening (SBVS) benchmarking study, from initial preparation to final evaluation.
Machine Learning Rescoring Process
This diagram details the specific process of applying machine learning scoring functions to refine the results of classical docking tools.
Table 4: Key Software Tools and Databases for Docking Benchmarking
| Resource Name | Type | Primary Function in Benchmarking | Relevant Citation |
|---|---|---|---|
| DEKOIS 2.0 | Benchmark Dataset | Provides sets of known active molecules and carefully matched decoys to test screening enrichment. | [31] |
| PDBbind | Database | A comprehensive collection of protein-ligand complexes with binding affinity data, used for scoring function validation. | [32] |
| CASF-2013 | Benchmark Dataset | A curated subset of PDBbind used for the Comparative Assessment of Scoring Functions. | [32] |
| AutoDock Vina | Docking Tool | A widely used, open-source molecular docking engine. | [31] |
| FRED | Docking Tool | A docking tool that requires pre-generated ligand conformations and uses a rigorous scoring process. | [31] |
| PLANTS | Docking Tool | A docking tool that utilizes ant colony optimization algorithms for pose prediction. | [31] |
| CNN-Score | ML Scoring Function | A convolutional neural network-based scoring function for re-ranking docking poses. | [31] |
| RF-Score-VS v2 | ML Scoring Function | A random forest-based scoring function designed for virtual screening. | [31] |
| TDC Docking Benchmark | Benchmark Framework | Provides benchmarks and oracles for evaluating AI-generated molecules against target proteins. | [35] |
| CCharPPI Server | Evaluation Tool | Allows for the assessment of scoring functions independent of the docking process itself. | [36] |
The application of artificial intelligence and machine learning (AI/ML) in drug discovery has ushered in a new era of computational methods research. Central to this paradigm shift is the critical need to rigorously benchmark the accuracy of different approaches, particularly in predicting drug mechanisms of action (MOA) in oncology. DeepTarget emerges as a significant innovation in this landscape, representing a class of models that prioritize functional cellular context over purely structural predictions. Unlike traditional structure-based methods that predict protein-small molecule binding affinity from static structures, DeepTarget introduces a fundamentally different approach by integrating large-scale drug and genetic knockdown viability screens with omics data from matched cell lines [37]. This methodological divergence presents a unique opportunity for comparative benchmarking to determine optimal applications for different computational strategies in target identification.
Methodological Comparison: DeepTarget Versus Structural Approaches
Core Computational Frameworks
The fundamental difference between DeepTarget and structure-based methods lies in their underlying principles and data requirements:
DeepTarget's Functional Approach: DeepTarget operates on the hypothesis that CRISPR-Cas9 knockout (CRISPR-KO) of a drug's target gene mimics the drug's inhibitory effects across cancer cell lines [37]. It integrates three data types across cancer cell line panels: (1) drug response profiles, (2) genome-wide CRISPR-KO viability profiles, and (3) corresponding omics data (gene expression and mutation) [37]. The method calculates a Drug-Knockout Similarity (DKS) score through linear regression that corrects for screen confounding factors, quantifying the similarity between drug treatment and genetic perturbation effects [37].
Structure-Based Methods: Tools like RoseTTAFold All-Atom and Chai-1 represent state-of-the-art in predicting protein-small molecule binding affinity based on structural information [37]. These methods rely on protein structures and chemical information to predict binding interactions but lack incorporation of cellular context, interaction dynamics, and pharmacokinetics [37].
Key Differentiating Factors
DeepTarget's architecture incorporates several distinctive capabilities that structure-based methods do not explicitly address:
- Context-Specific Secondary Target Prediction: DeepTarget identifies secondary targets that contribute to efficacy even when primary targets are present, and those mediating responses specifically when primary targets are not expressed [37].
- Mutation-Specificity Prediction: The tool determines whether drugs preferentially target wild-type or mutant protein forms by comparing DKS scores in different genetic contexts [37].
- Pathway-Level Effects: Beyond direct binding interactions, DeepTarget captures indirect, pathway-level effects that emerge from cellular context [37].
Experimental Benchmarking: Protocols and Performance Metrics
Gold-Standard Dataset Curation
To enable rigorous benchmarking, researchers curated eight gold-standard datasets comprising high-confidence drug-target pairs focused on cancer drugs [37]. These datasets represent distinct validation scenarios:
- Clinical Resistance Pairs: Drug-target pairs where tumor mutations cause clinical resistance (COSMIC resistance, N=16; oncoKB resistance, N=28) [37].
- FDA-Approved Pairs: Targets with FDA approval for anti-cancer treatment (FDA mutation-approval, N=86) [37].
- High-Confidence Experimental Pairs: Targets validated by multiple independent reports (BioGrid Highly Cited, N=28) or designated high-confidence by scientific advisory boards (SAB, N=24) [37].
- Direct Interaction Pairs: Compounds with confirmed direct target interactions (DrugBank Active Inhibitors, N=90; DrugBank Active Antagonists, N=52) [37].
- Selective Inhibitors: Highly selective inhibitors based on binding profiles (SelleckChem selective inhibitors, N=142) [37].
Quantitative Performance Comparison
In comprehensive benchmarking across the eight gold-standard datasets, DeepTarget demonstrated superior performance against state-of-the-art structural methods:
Table 1: Benchmarking Performance Across Methodologies
| Computational Method | Mean AUC Across 8 Datasets | Performance Advantage | Key Strength |
|---|---|---|---|
| DeepTarget | 0.73 | Reference standard | Cellular context integration |
| RoseTTAFold All-Atom | 0.58 | Outperformed in 7/8 datasets | Structural binding prediction |
| Chai-1 (without MSA) | 0.53 | Outperformed in 7/8 datasets | Protein-ligand interaction |
The benchmarking revealed that DeepTarget stratified positive versus negative drug-target pairs with significantly higher accuracy (mean AUC: 0.73) compared to RoseTTAFold All-Atom (0.58) and Chai-1 without multiple sequence alignment (0.53) [37]. DeepTarget outperformed these structural methods in 7 out of 8 tested datasets, demonstrating particularly strong performance in predicting clinically relevant targets and mutation-specific drug effects [37].
Experimental Validation Case Studies
Case Study 1: Ibrutinib in BTK-Negative Solid Tumors
Experimental Protocol: Researchers tested DeepTarget's prediction that Ibrutinib (FDA-approved for blood cancers) kills lung cancer cells through secondary targeting of epidermal growth factor receptor (EGFR) despite absence of its primary target Bruton's tyrosine kinase (BTK) [38] [39]. The validation involved comparing Ibrutinib effects on cancer cells with and without cancerous mutant EGFR [38] [39].
Results: Cells harboring the mutant EGFR form were significantly more sensitive to Ibrutinib, confirming EGFR as a functionally relevant target in this context [38] [39]. This demonstrated DeepTarget's ability to identify context-specific targets that explain drug efficacy in unexpected cellular environments.
Case Study 2: Pyrimethamine Repurposing
Experimental Protocol: Researchers experimentally validated DeepTarget's prediction that pyrimethamine, an anti-parasitic drug, affects cellular viability through modulation of mitochondrial function [40].
Results: The validation confirmed that pyrimethamine specifically affects the oxidative phosphorylation pathway, revealing a novel mechanism of action that could enable drug repurposing in oncology [40].
DeepTarget Workflow Methodology
Research Reagent Solutions for Implementation
Successful implementation of DeepTarget and comparable methods requires specific research reagents and computational resources:
Table 2: Essential Research Resources for DeepTarget Implementation
| Resource Category | Specific Requirements | Function in Methodology |
|---|---|---|
| Cell Line Panels | 371 cancer cell lines from DepMap | Provides cellular context diversity for pattern recognition |
| Genetic Screening Data | Chronos-processed CRISPR dependency scores | Controls for sgRNA efficacy, screen quality, copy number effects |
| Drug Response Profiles | 1,450 drug viability screens | Forms basis for drug-KO similarity comparisons |
| Omics Data | Gene expression and mutation profiles | Enables context-specific and mutation-specific analyses |
| Validation Assays | Cell viability assays, target modulation readouts | Experimental confirmation of computational predictions |
Signaling Pathways and Biological Mechanisms
DeepTarget's predictive power stems from its ability to capture pathway-level effects beyond direct binding interactions. The methodology inherently identifies drugs acting on several critical cancer pathways:
Pathway-Level Mechanisms Identified by DeepTarget
The tool has successfully clustered compounds by known mechanisms including inhibitors of EGFR, HDAC, MDM, MEK, MTOR, RAF, AKT, Aurora Kinases, CDK, CHK, PI3K, PARP, topoisomerase, and tubulin polymerization pathways based solely on DKS score patterns [37]. This demonstrates its capability to capture biologically meaningful pathway relationships without prior structural knowledge.
Discussion: Implications for Computational Methods Research
The benchmarking results position DeepTarget as a complementary approach to structure-based methods, each with distinct strengths and applications in drug discovery. While structural methods like RoseTTAFold All-Atom and Chai-1 excel at predicting direct binding interactions from protein structures, DeepTarget provides superior performance in predicting functional mechanisms of action in relevant cellular contexts [37]. This distinction is particularly valuable for:
- Drug Repurposing: Identifying novel mechanisms for existing drugs, as demonstrated with pyrimethamine [40].
- Context-Specific Efficacy: Understanding why drugs work in unexpected cellular environments, as shown with Ibrutinib in BTK-negative solid tumors [38] [39].
- Patient Stratification: Predicting mutation-specific drug effects for precision oncology applications [37].
- Secondary Target Identification: Systematically categorizing off-target effects as potential features rather than bugs [39].
The performance advantage of DeepTarget in real-world scenarios likely stems from its closer approximation of biological reality, where cellular context and pathway-level effects often play crucial roles beyond direct binding interactions [38]. However, structure-based methods retain value for early-stage binding prediction when cellular context data is unavailable.
The rigorous benchmarking of DeepTarget against structural methods establishes a new standard for evaluating computational target identification tools in oncology. By demonstrating superior performance across diverse validation datasets and experimental case studies, DeepTarget validates the importance of incorporating functional genomic data alongside chemical structural information. The methodology represents a significant advancement among target discovery methods that complements leading structure-based approaches by accounting for cellular context [37]. As the field progresses, the integration of both functional and structural approaches will likely provide the most comprehensive framework for accelerating drug development and repurposing efforts in oncology. Future benchmarking efforts should continue to expand the gold-standard datasets to include more diverse drug classes and cellular contexts to further refine our understanding of relative methodological strengths.
Accurate prediction of binding affinity between small molecules and protein targets is a cornerstone of computational drug design, as errors of even 1 kcal/mol can lead to erroneous conclusions about relative binding affinities, potentially derailing drug development pipelines [41]. Traditional empirical force fields and semi-empirical quantum methods often struggle to capture the complex quantum mechanical phenomena governing non-covalent interactions (NCIs) in ligand-pocket systems. While "gold standard" coupled cluster (CC) methods provide high accuracy for small systems, their application to biologically relevant ligand-pocket motifs remains computationally prohibitive [41]. Furthermore, puzzling disagreements between established quantum methods have cast doubt on the reliability of existing benchmarks for larger systems [41]. This review examines how emerging quantum-mechanical benchmarks are addressing these challenges by establishing robust "platinum standards" through the convergence of complementary high-level quantum methods, thereby providing reliable datasets for developing and validating faster computational approaches across the drug discovery workflow.
Established Benchmarking Frameworks and Their Limitations
Foundational Principles of Method Benchmarking
Rigorous benchmarking requires careful design to provide accurate, unbiased, and informative results [1]. Essential guidelines for high-quality benchmarking analyses include clearly defining the purpose and scope, comprehensive method selection, appropriate dataset choice, standardized evaluation metrics, and reproducible research practices [1]. Neutral benchmarking studies conducted independently of method development are particularly valuable for the research community, as they minimize perceived bias [1]. The selection of reference datasets represents a critical design choice, with simulated data offering known ground truth but requiring demonstration that simulations accurately reflect relevant properties of real data [1].
Data Leakage and Generalization Challenges in Existing Benchmarks
A critical issue undermining the reliability of binding affinity prediction models is train-test data leakage between widely used databases. Recent research has revealed substantial leakage between the PDBbind database and the Comparative Assessment of Scoring Function (CASF) benchmarks, with nearly 600 structural similarities detected between training and test complexes, affecting 49% of all CASF complexes [42]. This leakage enables models to achieve inflated performance metrics through memorization rather than genuine understanding of protein-ligand interactions [42]. Some models even perform comparably well on CASF benchmarks after omitting all protein or ligand information from their input data [42]. To address this, the PDBbind CleanSplit dataset has been developed using structure-based clustering algorithms that eliminate training complexes closely resembling CASF test complexes, ensuring strictly independent test sets for genuine generalization assessment [42].
Table 1: Established Benchmark Datasets for Binding Affinity Prediction
| Dataset Name | Size | Key Features | Primary Applications | Identified Limitations |
|---|---|---|---|---|
| PDBbind [42] | ~14,000 complexes (2020 version) | Experimentally determined structures with binding affinity data | Training deep learning models for affinity prediction | High similarity to CASF benchmarks causing data leakage |
| CASF Benchmark [42] | 285 complexes (2016 version) | Curated test set for scoring function evaluation | Comparative assessment of scoring functions | Structural similarities to PDBbind enable memorization |
| S66 & S66x8 [41] | 66 equilibrium + 528 non-equilibrium | Small molecular dimers with CCSD(T)/CBS reference | Testing methods on non-covalent interactions | Limited size and chemical diversity for drug discovery |
| QUID [41] | 170 systems (42 equilibrium + 128 non-equilibrium) | Drug-like molecules, multiple geometry points, "platinum standard" references | Benchmarking NCIs in realistic ligand-pocket motifs | Focused on model systems rather than full protein-ligand complexes |
The QUID Framework: A Quantum-Mechanical Benchmark for Ligand-Pocket Interactions
Design and Composition of the QUID Dataset
The "QUantum Interacting Dimer" (QUID) benchmark framework addresses critical gaps in existing datasets by providing 170 chemically diverse large molecular dimers of up to 64 atoms, incorporating H, N, C, O, F, P, S, and Cl elements that encompass most atom types relevant for drug discovery [41]. QUID was constructed through exhaustive exploration of different binding sites of nine large flexible chain-like drug molecules from the Aquamarine dataset, systematically probed with benzene (C6H6) and imidazole (C3H4N2) as representative ligand motifs [41]. The dataset includes both equilibrium geometries (42 dimers) and non-equilibrium conformations (128 dimers) sampled along non-covalent bond dissociation pathways, modeling snapshots of ligand binding to pockets [41].
The framework spans the three most frequent interaction types found on pocket-ligand surfaces: aliphatic-aromatic interactions, hydrogen bonding, and π-stacking [41]. The equilibrium dimers are categorized based on large monomer structural morphology: 'Linear' (retaining chain-like geometry), 'Semi-Folded' (partially bent sections), and 'Folded' (encapsulating the smaller monomer), thus modeling pockets with different packing densities [41]. This design produces a wide range of interaction energies from -24.3 to -5.5 kcal/mol at the PBE0+MBD level, with imidazole generally forming stronger non-covalent bonds than benzene [41].
Establishing the "Platinum Standard" Through Method Convergence
QUID introduces a "platinum standard" for ligand-pocket interaction energies achieved through tight agreement (0.3-0.5 kcal/mol) between two fundamentally different quantum methods: LNO-CCSD(T) and fixed-node diffusion Monte Carlo (FN-DMC) [41]. This convergence significantly reduces the uncertainty in highest-level QM calculations for larger systems, addressing previous disagreements between CC and QMC methods that had cast doubt on existing benchmarks [41]. The framework employs symmetry-adapted perturbation theory (SAPT) to decompose interaction energies into physically meaningful components (exchange-repulsion, electrostatic, induction, and dispersion), demonstrating that QUID broadly covers non-covalent binding motifs and energetic contributions relevant to biological systems [41].
Table 2: Quantum Methods in the QUID Benchmarking Framework
| Method Category | Specific Methods | Theoretical Basis | Role in QUID Benchmark | Computational Cost |
|---|---|---|---|---|
| Platinum Standard | LNO-CCSD(T)/CBS, FN-DMC | Localized natural orbital coupled cluster with complete basis set; Fixed-node diffusion Monte Carlo | Reference values through method convergence | Extremely high (prohibitive for routine use) |
| Density Functional Theory | PBE0+MBD, other dispersion-inclusive DFAs | Kohn-Sham equations with approximate exchange-correlation functionals | Geometry optimization and performance evaluation | Medium to high (feasible for many systems) |
| SAPT | Symmetry-Adapted Perturbation Theory | Energy component decomposition based on perturbation theory | Analysis of interaction energy contributions | Medium (depends on implementation) |
| Semiempirical Methods | GFN2-xTB, PM6-D3H4, OM2 | Approximate quantum chemistry with parameterized integrals | Performance assessment for fast methods | Low (applicable to very large systems) |
| Force Fields | GAFF, C36, GFN-FF | Empirical potentials with parameterized interactions | Performance evaluation of classical simulations | Very low (suitable for molecular dynamics) |
Performance Comparison Across Computational Methods
Quantum and Classical Electronic Structure Methods
Analysis of method performance on the QUID benchmark reveals that several dispersion-inclusive density functional approximations (DFAs) provide accurate energy predictions close to the platinum standard references, achieving performance comparable to much more expensive wavefunction methods for many systems [41]. However, these DFAs exhibit significant discrepancies in the magnitude and orientation of atomic van der Waals forces, which could substantially influence the dynamics of ligands within binding pockets despite accurate energy predictions [41]. This force discrepancy highlights the importance of evaluating force accuracy in addition to energy accuracy when developing methods for molecular dynamics simulations.
Semiempirical quantum methods and widely used empirical force fields require substantial improvements, particularly in capturing non-covalent interactions for out-of-equilibrium geometries [41]. These methods struggle with the diverse NCI patterns present in the QUID dataset, limiting their reliability for predicting binding affinities in drug discovery applications without significant parameter refinement.
Emerging Quantum-Inspired and Machine Learning Approaches
Hybrid quantum-classical neural networks represent an emerging approach that reduces model complexity while maintaining predictive performance. Recent work demonstrates that replacing the first convolutional layer in a 3D CNN with a quantum circuit can reduce training parameters by 20% while maintaining classical CNN performance, with training time reductions of 20-40% depending on hardware [43]. These hybrid models show particular promise for handling the growing size of structural databases in drug discovery.
For graph neural networks (GNNs), rigorous benchmarking on leakage-free splits is essential. When state-of-the-art models like GenScore and Pafnucy were retrained on the PDBbind CleanSplit dataset with reduced data leakage, their performance dropped markedly, confirming that previously reported high scores were largely driven by data leakage rather than genuine generalization [42]. In contrast, the GEMS (Graph neural network for Efficient Molecular Scoring) model maintains robust performance when trained on CleanSplit, leveraging sparse graph modeling of protein-ligand interactions and transfer learning from language models [42].
Table 3: Performance Comparison Across Method Categories
| Method Type | Representative Examples | Key Strengths | Key Limitations | Recommended Use Cases |
|---|---|---|---|---|
| Wavefunction Methods | LNO-CCSD(T), FN-DMC [41] | Highest achievable accuracy, rigorous theoretical foundation | Computationally prohibitive for most systems | Generating reference data, small system validation |
| Density Functional Theory | PBE0+MBD, ωB97M-V [41] | Favorable accuracy-cost balance for medium systems | Force inaccuracies, functional transferability issues | Binding mode prediction, medium system screening |
| Semiempirical QM | GFN2-xTB, PM6-D3H4 [41] | Fast quantum mechanical calculations | Poor performance for out-of-equilibrium geometries | Preliminary screening of very large compound libraries |
| Force Fields | GAFF, C36 [41] | Nanosecond to microsecond molecular dynamics | Limited transferability, inaccurate for complex NCIs | Conformational sampling, explicit solvent effects |
| Machine Learning | GEMS, Hybrid QCNNs [42] [43] | High speed once trained, improving accuracy | Data quality dependence, generalization concerns | High-throughput virtual screening, lead optimization |
Experimental Protocols and Workflows
QUID Benchmark Generation Protocol
The QUID dataset generation follows a systematic protocol beginning with selection of nine chemically diverse drug-like molecules (approximately 50 atoms each) with flexible chain-like geometries from the Aquamarine dataset [41]. For each large monomer, binding sites are probed with two small monomers (benzene and imidazole) representing common ligand motifs, initially positioned with aromatic rings aligned at 3.55±0.05 Å from binding site aromatic rings [41]. Dimer structures are then optimized at the PBE0+MBD level of theory, resulting in 42 equilibrium dimers categorized by structural morphology [41].
For non-equilibrium conformations, a representative selection of 16 dimers is used to construct dissociation pathways along π-π or H-bond vectors using eight multiplicative distance factors (q = 0.90, 0.95, 1.00, 1.05, 1.10, 1.25, 1.50, 1.75, 2.00), where q=1.00 represents the equilibrium dimer [41]. Structures at each distance are optimized with heavy atoms of the small monomer and corresponding binding site frozen, generating 128 non-equilibrium conformations that model binding process snapshots [41].
Reference interaction energies are computed using both LNO-CCSD(T)/CBS and FN-DMC methods, with agreement within 0.3-0.5 kcal/mol establishing the platinum standard reference values [41]. SAPT calculations further decompose interaction energies into physical components for mechanistic insights [41].
Quantum Resource Estimation for Binding Affinity Calculations
For metalloprotein systems like amyloid-beta with metal ions, quantum computers show potential for accelerating binding affinity calculations, but require substantial resources. A detailed workflow for amyloid-beta binding to metal ions involves: (1) obtaining initial geometry from experimental databases like PDB; (2) coarse optimization using classical force fields; (3) refinement with QM/MM methods; (4) fragmentation using the Fragment Molecular Orbital method; and (5) high-accuracy energy calculation for fragments using quantum phase estimation or full configuration interaction algorithms [44].
Resource estimates for the AB16 protein (PDB ID: 1ZE9) indicate 15 fragments after division, with the metal-binding fragments representing the most computationally challenging components [44]. While fault-tolerant quantum computers could potentially solve these strongly correlated problems more efficiently than classical computers, current quantum hardware remains limited by noise and qubit counts [44].
Figure 1: Workflow for Quantum-Accurate Binding Affinity Calculation. This diagram illustrates the integrated classical-quantum workflow for high-accuracy binding affinity prediction, highlighting where quantum computation provides potential advantages for strongly correlated systems.
Benchmark Datasets and Reference Data
- QUID Dataset: Provides 170 molecular dimers with "platinum standard" interaction energies from convergent LNO-CCSD(T) and FN-DMC calculations for benchmarking NCIs in drug-like systems [41].
- PDBbind CleanSplit: A carefully filtered version of PDBbind that eliminates train-test data leakage, enabling genuine assessment of model generalization capability [42].
- CASF Benchmark: The Comparative Assessment of Scoring Functions benchmark, though requiring caution regarding data leakage, remains widely used for scoring function evaluation [42].
- S66 and S66x8: Well-established datasets of 66 equilibrium and 528 non-equilibrium small molecular dimers with CCSD(T)/CBS reference values for non-covalent interactions [41].
Software and Computational Methods
- LNO-CCSD(T): Localized natural orbital coupled cluster implementation that extends the applicability of CCSD(T) to larger systems while maintaining high accuracy [41].
- FN-DMC: Fixed-node diffusion Monte Carlo as a complementary quantum method to establish benchmark convergence with LNO-CCSD(T) [41].
- GEMS: Graph neural network for Efficient Molecular Scoring that maintains performance on leakage-free benchmarks through sparse graph modeling and transfer learning [42].
- Hybrid Quantum-Classical CNNs: Convolutional neural networks with quantum circuit layers that reduce parameter counts while maintaining prediction accuracy [43].
Analysis and Validation Tools
- SAPT: Symmetry-Adapted Perturbation Theory for decomposing interaction energies into physical components (electrostatics, exchange-repulsion, induction, dispersion) [41].
- Structure-Based Clustering Algorithms: Methods for identifying structural similarities between protein-ligand complexes to detect data leakage and ensure dataset independence [42].
- Applicability Domain Assessment: Tools for evaluating whether query compounds fall within the chemical space covered by model training data [45].
The establishment of robust quantum-mechanical benchmarks like QUID represents a significant advancement toward reliable binding affinity prediction in computational drug design. By achieving convergence between complementary high-level quantum methods, these benchmarks provide trustworthy reference data for developing and validating faster computational approaches. The identification and remediation of data leakage issues in widely used benchmarks further strengthens the foundation for method development.
Future progress will likely involve several key directions: (1) expansion of benchmark systems to include more diverse protein targets and ligand chemotypes; (2) development of multi-fidelity benchmarks that enable method evaluation across accuracy-cost tradeoffs; (3) integration of quantum benchmarks with experimental validation for complementary verification; and (4) continued refinement of quantum-inspired algorithms that balance accuracy with computational feasibility for industry-scale applications. As these benchmarks mature and computational methods improve, the role of high-accuracy binding affinity prediction will expand throughout the drug discovery pipeline, from target identification to lead optimization, potentially reducing reliance on costly experimental screening while accelerating therapeutic development.
Overcoming Pitfalls: A Guide to Error Reduction and Model Optimization
In computational chemistry, the evolution of Quantitative Structure-Activity Relationship (QSAR) modeling exemplifies how methodological rigor and benchmarking separate predictive successes from costly failures. As the field progresses, traditional approaches like 2D-QSAR have become obsolete, superseded by more sophisticated multidimensional methods. Within the broader thesis of benchmarking density of states (DOS) accuracy across computational methods research, this guide examines the specific failure modes of outdated QSAR methodologies. For drug discovery researchers and development professionals, understanding these pitfalls is crucial for allocating resources effectively and building models that deliver genuine predictive power rather than statistical illusions. This analysis draws on current benchmarking studies to objectively compare methodological performance and provide the experimental protocols needed to validate computational approaches in real-world scenarios.
Section 1: The Obsolescence of 2D-QSAR in Modern Drug Discovery
The Documented Decline of 2D Descriptors
Market analyses and expert consensus clearly indicate that simple two-dimensional QSAR models are now largely considered obsolete and are often rejected by scientific journals [46]. The fundamental limitation of 2D-QSAR lies in its inability to capture the spatial and electronic properties that govern molecular interactions in three-dimensional space. While 2D descriptors like molecular weight and atom counts provide basic information, they completely miss the critical structural arrangements that determine binding affinity and specificity.
The evolution in molecular descriptors has paralleled that of QSAR methodologies, with a definitive move toward more sophisticated and information-rich descriptors [46]. These include 3D descriptors that capture the spatial arrangement of atoms and quantum mechanical descriptors that describe electronic properties—features completely absent in traditional 2D approaches.
Experimental Evidence: The Performance Gap in Direct Comparisons
Rigorous benchmarking studies provide quantitative evidence of 2D-QSAR's limitations. A comprehensive study on Imatinib derivatives developed an ensemble of QSAR models relying on deep neural nets (DNN) and hybrid sets of 2D/3D/MD descriptors to predict binding affinity and inhibition potencies [47]. Through strict validation protocols based on external test sets and 10-fold native and nested cross-validations, researchers made a critical discovery: incorporating additional 3D protein-ligand binding site fingerprint descriptors or MD time-series descriptors did not significantly improve the overall R² but consistently lowered the Mean Absolute Error (MAE) of DNN QSAR models [47].
Table 1: Performance Comparison of QSAR Approaches for Imatinib Derivatives
| Descriptor Set | Dataset | Sample Size | R² | Mean Absolute Error |
|---|---|---|---|---|
| 2D Only | pKi | n = 555 | ≥ 0.71 | ≤ 0.85 |
| 2D/3D/MD Hybrid | pKi | n = 555 | ≥ 0.71 | < 0.85 |
| 2D Only | pIC50 | n = 306 | ≥ 0.54 | ≤ 0.71 |
| 2D/3D/MD Hybrid | pIC50 | n = 306 | ≥ 0.54 | < 0.71 |
This seemingly subtle improvement in MAE proves critically important in practical drug discovery applications where accurately predicting the magnitude of activity directly impacts compound prioritization and optimization strategies. The augmented models incorporating 3D and dynamics descriptors provided the additional benefit of identifying and understanding key dynamic protein-ligand interactions to be optimized for further molecular design [47]—a capability completely absent in 2D-QSAR approaches.
Section 2: Beyond 2D-QSAR: Current Methodological Pitfalls in Computational Drug Discovery
The Data Quality Foundation: Garbage In, Gospel Out
Perhaps the most pervasive methodological error in QSAR modeling involves inadequate chemical structure standardization. The predictivity and accuracy of developed models highly depend upon the quality of the training data, and failure to properly curate molecular structure representations has negative consequences on property prediction, classification, registration, deduplication, and similarity searches [48].
Common structure standardization issues include:
- Tautomerization inconsistencies: The same compound represented in different tautomeric forms
- Salt handling irregularities: The same molecular entity represented with and without counterions
- Stereochemistry errors: Improper representation of chiral centers and geometric isomers
- Functional group representation: Inconsistent depiction of groups like nitro and azo compounds
Automated "QSAR-ready" workflows have been developed to address these concerns through systematic operations including desalting, stripping of stereochemistry (for 2D structures), standardization of tautomers and nitro groups, valence correction, and neutralization when possible [48]. The implementation of such standardized workflows is now considered essential for collaborative QSAR projects to ensure consistency of results across different participants.
Benchmarking Fallacies: Mismatches Between Validation and Real-World Applications
The CARA (Compound Activity benchmark for Real-world Applications) study revealed that existing benchmark datasets frequently fail to match real-world scenarios where experimentally measured data are generally sparse, unbalanced, and from multiple sources [49]. Through careful analysis of ChEMBL data, researchers identified two distinct patterns in compound activity data that correspond to different drug discovery stages:
- Virtual Screening (VS) Assays: Exhibit diffused distribution patterns with lower pairwise compound similarities, representative of diverse compound libraries
- Lead Optimization (LO) Assays: Show aggregated distribution patterns with high compound similarities, characteristic of congeneric series
This distinction proves critically important because models that perform well on one assay type may fail miserably on the other. Unfortunately, most existing benchmarks do not properly distinguish between these fundamentally different application scenarios, leading to overestimated model performance and poor real-world transferability.
Improper Validation Protocols: The Temporal Realism Gap
A comprehensive review of drug discovery benchmarking practices reveals that most protocols rely on k-fold cross-validation, with limited application of more rigorous "temporal splits" (splitting based on approval dates) [50]. This creates a fundamental validity gap—models tested on compounds that existed when the model was trained perform artificially well compared to their real-world performance on truly novel chemical entities discovered after model development.
The heavy reliance on area under the receiver-operating characteristic curve (AUROC) and area under the precision-recall curve (AUPRC) as primary metrics has also been questioned for relevance to actual drug discovery decisions [50]. More interpretable metrics like recall, precision, and accuracy above specific activity thresholds often provide more actionable insights for medicinal chemistry optimization campaigns.
Section 3: Experimental Protocols for Robust QSAR Benchmarking
Standardized Workflow for "QSAR-Ready" Structure Preparation
Objective: To generate standardized chemical structure representations suitable for descriptor calculation and modeling, ensuring consistency and reproducibility across QSAR studies.
Materials and Software:
- KNIME Analytics Platform with chemistry plug-ins
- "QSAR-ready" workflow (publicly available in KNIME, GitHub, and docker containers)
- Input chemical structures in SMILES, InChI, or SDF formats
Procedure:
- Structure Input: Read structure encodings and cross-reference with existing identifiers for consistency
- Desalting: Remove counterions and salts, retaining the primary molecular structure
- Stereochemistry Handling: Strip stereochemistry for 2D-QSAR; standardize for 3D-QSAR
- Tautomer Standardization: Apply rules to represent tautomers consistently
- Functional Group Normalization: Standardize representation of nitro groups and other functional groups
- Valence Correction: Identify and correct invalid valences
- Neutralization: Neutralize structures when possible (protocol-dependent)
- Duplicate Removal: Identify and remove duplicate structures
- Output: Generate standardized "QSAR-ready" structures for descriptor calculation
Validation: The workflow should be validated using reference datasets with known standardization challenges, with output verified by manual inspection of problematic cases [48].
Task-Aware Benchmarking Protocol for Compound Activity Prediction
Objective: To evaluate QSAR model performance under conditions that mirror real-world drug discovery scenarios.
Materials:
- Curated assay data from ChEMBL or similar databases
- Clearly defined VS and LO assay classifications based on compound similarity distributions
- Multiple state-of-the-art machine learning and deep learning methods for comparison
Procedure:
- Data Curation and Classification:
- Retrieve compound activity data grouped by assay ID
- Calculate pairwise compound similarities within each assay
- Classify assays as VS-type (diffused pattern) or LO-type (aggregated pattern) based on similarity distributions
Task-Appropriate Data Splitting:
- For VS tasks: Apply random splitting or scaffold-based splitting
- For LO tasks: Implement time-split or series-based splitting where compounds from the same series are kept together
Model Training and Evaluation:
- Train models using standardized protocols across all methods
- Evaluate performance separately on VS and LO test sets
- Apply comprehensive metrics including MAE, R², AUROC, AUPRC, and task-specific metrics
Robustness Testing:
- Test models on external validation sets with temporal separation
- Evaluate performance on activity cliffs and challenging edge cases
- Assess uncertainty calibration and confidence estimation
Analysis: Compare model performance across different assay types and splitting methods, identifying methods that maintain performance under realistic conditions [49].
Table 2: Essential Research Reagents and Computational Tools for Robust QSAR
| Category | Specific Tool/Resource | Function and Application | Key Considerations |
|---|---|---|---|
| Descriptor Calculation | 3D Protein-Ligand Binding Site Fingerprints | Captures spatial interactions in binding sites | Requires reliable 3D structure data |
| MD Time-Series Descriptors | Incorporates dynamic structural information | Computationally intensive | |
| Benchmarking Datasets | CARA Benchmark | Evaluates real-world applicability | Distinguishes VS vs. LO assays |
| Imatinib Derivatives Data | Direct comparison of 2D/3D/MD approaches | Well-characterized public dataset | |
| Structure Standardization | QSAR-ready KNIME Workflow | Automated structure curation | Essential for reproducible descriptors |
| CVSP Platform | Online structure validation | Useful for custom standardization rules | |
| Validation Frameworks | Temporal Splitting | Assesses performance on novel chemotypes | Mimics real discovery scenarios |
| Activity Cliff Detection | Tests performance on challenging cases | Identifies extrapolation limitations |
Section 4: Visualization of Methodological Relationships and Workflows
QSAR Methodology Evolution from Obsolete to Modern Approaches
The evidence from contemporary benchmarking studies clearly demonstrates that 2D-QSAR approaches have been rendered obsolete by more sophisticated multidimensional methodologies. Beyond this fundamental shift, researchers must address multiple additional failure modes including inadequate structure standardization, improperly designed benchmarks that don't reflect real-world applications, and validation protocols that overestimate practical utility. The experimental protocols and benchmarking frameworks presented here provide a pathway for developing QSAR models that deliver genuine predictive value in drug discovery. As the field continues evolving with advances in artificial intelligence and molecular dynamics, maintaining rigorous methodological standards and appropriate benchmarking practices will remain essential for distinguishing true predictive advances from statistical artifacts.
In computational methods research, the accuracy of any predictive model is fundamentally constrained by the quality and consistency of the data on which it is built. This is particularly critical in fields like drug development and materials science, where decisions rely on the predictive performance of Digital Outcome Simulations (DOS). The benchmarking of DOS accuracy across computational methods is not merely a software challenge but a data curation challenge. This guide objectively compares methodologies and tools for two pillars of robust data curation: the treatment of outliers and the standardization of diverse chemical inputs. We summarize performance data from independent benchmarking studies to provide researchers, scientists, and drug development professionals with evidence-based recommendations for their workflows.
Benchmarking Outlier Treatment Methods
Outliers—data points that deviate significantly from other observations—can arise from experimental errors, rare biological events, or data processing mistakes. Their presence can skew model training and lead to inaccurate predictions. The choice of treatment method is therefore crucial.
Performance Comparison of Statistical Methods
Independent benchmarking efforts often evaluate outlier detection methods on their precision and computational efficiency. The following table summarizes the core characteristics and typical application contexts of common statistical techniques.
Table 1: Comparison of Common Statistical Outlier Treatment Methods
| Method | Mechanism | Performance & Best Use-Cases | Key Limitations |
|---|---|---|---|
| Z-Score | Measures the number of standard deviations a point is from the mean [51]. | Simple and efficient for large, normally distributed datasets. Effective at flagging extreme global outliers. | Assumes normal distribution; performance degrades with skewed data. Sensitive to the presence of other outliers [51]. |
| IQR (Interquartile Range) | Defines outliers as points below Q1 - 1.5×IQR or above Q3 + 1.5×IQR [51]. | Non-parametric; robust to non-normal distributions. Widely used for its simplicity and effectiveness on a wide range of data types. | May not be sensitive enough for high-dimensional data where outliers are more complex. |
| Tukey's Fences | A variation of IQR that can use different multipliers (e.g., 3.0 for extreme outliers) to adjust sensitivity [51]. | Provides a tiered approach for defining "mild" and "extreme" outliers, offering more granular control than the standard IQR method. | Same fundamental limitations as the IQR method, as it is based on the same core principle. |
Experimental Protocols for Outlier Detection
A typical workflow for implementing these methods, as utilized in benchmarking studies, involves a defined series of steps to ensure reproducibility and validity [45] [52]:
- Data Preprocessing: The dataset is cleaned to handle missing values and ensure consistency in formatting and units.
- Method Application: The chosen statistical method (e.g., Z-score with a threshold of 3 or IQR) is applied to the preprocessed data to flag potential outliers.
- Visual Inspection: The results are often visualized using scatter plots, box plots, or PCA plots to contextualize the flagged points and identify any obvious patterns.
- Expert Validation: Flagged outliers are reviewed by a domain expert to distinguish between data errors (for removal or correction) and rare but valid biological or chemical phenomena (for retention).
- Impact Assessment: The model is trained on both the raw and the curated dataset, and the performance on a held-out test set is compared to quantify the impact of outlier treatment.
Standardizing Chemical Inputs: A Tool Performance Benchmark
The predictive power of Quantitative Structure-Activity Relationship (QSAR) models hinges on the quality and standardization of the input chemical structures. Inconsistent representation of chemical structures is a major source of noise and error. A comprehensive 2024 benchmarking study evaluated twelve software tools for predicting physicochemical and toxicokinetic properties, emphasizing the critical role of data curation [45].
Performance of Standardization and QSAR Tools
The study collected 41 validation datasets from the literature, which were rigorously curated. The curation process involved standardizing chemical structures, neutralizing salts, removing duplicates and inorganic compounds, and resolving inconsistent property values across datasets [45]. The following table summarizes the findings for selected high-performing tools.
Table 2: Benchmarking Performance of Selected Chemical Property Prediction Tools
| Software Tool | Property Type | Reported Performance (R² / Balanced Accuracy) | Key Strengths & Notes |
|---|---|---|---|
| OPERA | Physicochemical (PC) | R² average: 0.717 (for PC properties) | Open-source; provides applicability domain assessment; models showed adequate predictive performance [45]. |
| Proprietary Tool A | Toxicokinetic (TK) - Classification | Avg. Balanced Accuracy: 0.780 (for TK properties) | Freely available; demonstrated good predictivity for classification tasks like metabolic stability [45]. |
| Proprietary Tool B | Toxicokinetic (TK) - Regression | R² average: 0.639 (for TK regression) | Freely available; reliable performance for regression tasks like volume of distribution [45]. |
The benchmarking concluded that while models for physicochemical properties generally outperformed those for toxicokinetic properties, several tools demonstrated robust and reliable predictive performance, making them suitable for high-throughput assessment [45].
Experimental Protocol for Chemical Standardization
The benchmarking study employed a rigorous, automated protocol for chemical data curation, which is essential for reproducible results [45]:
- Structure Retrieval: For substances lacking a SMILES string, isomeric SMILES were retrieved from databases like PubChem using CAS numbers or chemical names.
- Standardization: An automated procedure using the RDKit Python package was applied to all structures. This involved:
- Neutralizing salts.
- Removing inorganic and organometallic compounds.
- Eliminating duplicates at the SMILES level.
- Data Verification: Experimental data was curated to exclude "intra-outliers" (potential annotation errors within a single dataset identified by a Z-score > 3) and "inter-outliers" (compounds with inconsistent values across different datasets for the same property) [45].
- Applicability Domain (AD) Assessment: Predictions were evaluated with an emphasis on those falling within the model's applicability domain, as performance is typically more reliable for these compounds [45].
Integrated Workflow for Robust Data Curation
Combining the practices of outlier treatment and chemical standardization into a single, logical workflow ensures that data entering a DOS model is of the highest possible integrity. The following diagram illustrates this integrated process.
Integrated Data Curation Workflow
The Scientist's Toolkit: Essential Research Reagents & Solutions
The following table details key computational tools and resources that form the foundation of a rigorous data curation pipeline for chemical and biological data.
Table 3: Essential Research Reagents & Computational Solutions for Data Curation
| Tool / Resource | Function | Relevance to Curation |
|---|---|---|
| RDKit | An open-source cheminformatics toolkit [45]. | Used for standardizing chemical structures, converting file formats, and calculating molecular descriptors. Essential for the chemical standardization protocol. |
| PubChem PUG API | A programming interface for the PubChem database [45]. | Used to retrieve canonical or isomeric SMILES from chemical names or CAS numbers, ensuring consistent structural representation. |
| JARVIS-Leaderboard | An open-source benchmarking platform for materials design methods [53]. | Provides a community-driven resource to compare the performance of various computational methods, including AI and force-fields, against standardized benchmarks. |
| LightlyOne | A commercial data curation platform for machine learning [54]. | Uses self-supervised learning to compute image embeddings, enabling the identification of duplicates and selection of diverse, informative data subsets for model training. |
| MedDRA | (Medical Dictionary for Regulatory Activities) A standardized medical terminology dictionary [55] [56]. | Critical for curating clinical trial data, ensuring consistent coding of adverse events and other medical information across studies. |
The benchmarking data and experimental protocols presented here underscore a critical theme: the accuracy of Digital Outcome Simulations is inseparable from the rigor of the underlying data curation. There is no single "best" method for all scenarios; the choice between outlier treatment techniques depends on the data distribution and the research question, while the selection of chemical standardization tools is guided by the specific properties of interest. By adopting the integrated workflow and best practices outlined in this guide—validating outlier treatment decisions with domain knowledge, rigorously standardizing chemical inputs, and leveraging community benchmarks—researchers can significantly enhance the reliability, reproducibility, and predictive power of their computational methods.
In computational research, the accuracy and reliability of machine learning (ML) and deep learning (DL) models are critical for advancements in fields ranging from cybersecurity to drug discovery. The performance of these models is not solely dependent on the choice of algorithm but is profoundly influenced by two crucial preparatory processes: feature selection and hyperparameter tuning. Feature selection involves identifying the most relevant variables from the dataset to reduce dimensionality and enhance model generalization, while hyperparameter tuning focuses on optimizing the external configuration settings of algorithms to maximize predictive performance. Within the specific context of benchmarking Denial-of-Service (DoS) attack detection accuracy across computational methods, these processes become paramount for developing systems capable of accurately distinguishing malicious traffic from legitimate network behavior. This guide objectively compares the performance of various feature selection and hyperparameter tuning methodologies, providing supporting experimental data to inform researchers, scientists, and drug development professionals about optimal strategies for model optimization.
Comparative Analysis of Methodologies and Performance
The effectiveness of feature selection and hyperparameter tuning techniques is best demonstrated through direct comparison of their application in real-world research scenarios. The table below summarizes performance outcomes from recent studies across cybersecurity and pharmaceutical domains.
Table 1: Performance Comparison of Optimization Techniques Across Domains
| Domain | Feature Selection Method | Hyperparameter Tuning Method | Model | Key Performance Metrics |
|---|---|---|---|---|
| Network Security | Backward Elimination + Recursive Feature Elimination | Grid Search (CV=5) | Random Forest | 99.99% accuracy, 99.99% F1-score [57] |
| IoT Security | Coati-Grey Wolf Optimization (CGWO) | Improved Chaos African Vulture Optimization (ICAVO) | Conditional Variational Autoencoder | 99.91% accuracy [58] |
| DoS Attack Detection | Not specified | Adaptive GridSearchCV | SVM | 99.87% accuracy, 28% reduced execution time [59] |
| Drug Discovery | Not specified | Hierarchically Self-Adaptive PSO | Stacked Autoencoder | 95.52% accuracy, 0.010s/sample computational complexity [60] |
| LDDoS Attack Detection | Wrapper-based method | Not specified | Lightweight Deep Network | 99.77% accuracy, 95.45% F1-score [18] |
| DoS Attack Detection | Not specified | Probability-based predictions + Sequential analysis | Hybrid LSTM-SVM | 97% accuracy [61] |
| Pharmaceutical Research | Not specified | Bayesian Optimization | Stacking Ensemble | R²: 0.92, MAE: 0.062 [62] |
The data reveals that the most significant accuracy improvements occur when feature selection and hyperparameter tuning are systematically combined. The highest-performing model in network security employed Backward Elimination with Recursive Feature Elimination for feature selection and Grid Search with 5-fold Cross-Validation for hyperparameter tuning, achieving exceptional performance metrics [57]. Similarly, in IoT security, the integration of Coati-Grey Wolf Optimization for feature selection with an Improved Chaos African Vulture Optimization algorithm for parameter adjustment yielded near-perfect accuracy [58]. These results underscore the synergistic effect of combining robust feature selection with systematic hyperparameter optimization.
Impact on Model Generalization and Computational Efficiency
Beyond raw accuracy, these optimization techniques significantly impact model generalization and computational efficiency. The Adaptive GridSearchCV approach for DDoS detection not only maintained high accuracy but also reduced execution time by 28% for SVM models and up to 63% for KNN models compared to standard GridSearchCV [59]. In drug discovery, the Hierarchically Self-Adaptive Particle Swarm Optimization (HSAPSO) method demonstrated exceptional computational efficiency with minimal processing time per sample while maintaining high stability (±0.003) [60]. These findings highlight that proper parameter optimization enhances both performance and practical deployment feasibility, particularly important in resource-constrained environments like IoT security and large-scale pharmaceutical research.
Detailed Experimental Protocols
Random Forest with Backward Elimination and Grid Search
Objective: To classify DDoS attacks using an optimized Random Forest model through feature selection and hyperparameter tuning [57].
Dataset: DDoS-SDN dataset containing network traffic features.
Methodology:
- Feature Selection: Implement Backward Elimination (BE) and Recursive Feature Elimination (RFE) to identify the most discriminative features for DDoS classification.
- Data Splitting: Partition data into training and testing sets using standard 70-30 or 80-20 splits.
- Hyperparameter Tuning: Apply Grid Search with 5-fold Cross-Validation (CV=5) to optimize Random Forest parameters including:
- Number of trees in the forest (nestimators)
- Maximum depth of trees (maxdepth)
- Minimum samples required to split a node (minsamplessplit)
- Minimum samples required at each leaf node (minsamplesleaf)
- Model Training: Train Random Forest classifier with optimized feature set and hyperparameters.
- Validation: Evaluate model performance on unseen test data using accuracy, precision, recall, and F1-score.
Key Findings: The optimized model achieved 99.99% accuracy, outperforming baseline classifiers including Naive Bayes (98.85%), K-Nearest Neighbors (97.90%), and Support Vector Machine (95.70%) [57].
TTOS-RAAM Model for IoT Security
Objective: To recognize adversarial attack behavior in IoT networks using a Two-Tier Optimization Strategy for Robust Adversarial Attack Mitigation (TTOS-RAAM) [58].
Dataset: RT-IoT2022 dataset containing IoT network traffic data.
Methodology:
- Data Preprocessing: Apply min-max scaler to normalize input data into a uniform format.
- Feature Selection: Implement hybrid Coati-Grey Wolf Optimization (CGWO) approach to select optimal features for attack detection.
- Attack Detection: Employ Conditional Variational Autoencoder (CVAE) to detect adversarial attacks by identifying anomalous patterns.
- Parameter Optimization: Utilize Improved Chaos African Vulture Optimization (ICAVO) for parameter adjustment of the CVAE model.
- Validation: Conduct comprehensive experimentation analysis under multiple aspects to evaluate detection performance.
Key Findings: The TTOS-RAAM technique achieved a superior accuracy value of 99.91%, demonstrating effectiveness in IoT adversarial attack detection [58].
Stacked Autoencoder with HSAPSO for Drug Classification
Objective: To classify drug targets using an optimized Stacked Autoencoder with adaptive parameter optimization [60].
Dataset: Curated datasets from DrugBank and Swiss-Prot containing pharmaceutical compounds and target information.
Methodology:
- Data Preprocessing: Perform rigorous preprocessing to ensure input data quality and consistency.
- Feature Extraction: Utilize Stacked Autoencoder (SAE) for robust feature extraction from molecular data.
- Hyperparameter Optimization: Implement Hierarchically Self-Adaptive Particle Swarm Optimization (HSAPSO) to fine-tune SAE hyperparameters including:
- Number of hidden layers
- Nodes per layer
- Learning rate
- Regularization parameters
- Model Training: Train the classification model using optimized architecture.
- Validation: Evaluate performance on validation and unseen test sets using accuracy, computational complexity, and stability metrics.
Key Findings: The framework achieved 95.52% accuracy with significantly reduced computational complexity (0.010s per sample) and exceptional stability (±0.003) [60].
Visualizing Optimization Workflows
The following diagrams illustrate the key workflows for integrating feature selection and hyperparameter tuning in model optimization pipelines.
Integrated Feature Selection and Hyperparameter Tuning Workflow
Integrated Optimization Workflow
This diagram illustrates the synergistic relationship between feature selection and hyperparameter tuning. The process begins with raw dataset preparation, followed by simultaneous feature selection and hyperparameter optimization. The selected features and tuned parameters are then used for model training, with performance evaluation feeding back into iterative refinement of both processes [58] [57] [60].
Hyperparameter Tuning Decision Framework
Hyperparameter Tuning Method Selection
This decision framework outlines the selection criteria for different hyperparameter tuning methodologies. The choice depends on several factors including the number of hyperparameters, available computational resources, time constraints, and performance requirements [63]. For small models with expert knowledge available, manual tuning may suffice, while Grid Search is suitable for small parameter spaces. Random Search works well for large parameter spaces, Bayesian Optimization for high computational cost scenarios, and Hyperband for resource-constrained environments [63] [59].
The Researcher's Toolkit: Essential Research Reagent Solutions
Table 2: Essential Research Reagents for Optimization Experiments
| Research Reagent | Function | Example Applications |
|---|---|---|
| GridSearchCV | Exhaustive hyperparameter search over specified values | Systematic parameter optimization for ML models [57] [59] |
| Adaptive GridSearchCV | Enhanced GridSearch with improved computational efficiency | DDoS detection with reduced execution time [59] |
| Bayesian Optimization | Probabilistic model-based hyperparameter optimization | Drug discovery PK parameter prediction [62] |
| Coati-Grey Wolf Optimization (CGWO) | Hybrid bio-inspired feature selection | IoT adversarial attack detection [58] |
| Hierarchically Self-Adaptive PSO (HSAPSO) | Adaptive parameter optimization inspired by swarm behavior | Drug classification and target identification [60] |
| Improved Chaos African Vulture Optimization (ICAVO) | Nature-inspired parameter adjustment | IoT network security model tuning [58] |
| Recursive Feature Elimination (RFE) | Iterative feature selection by eliminating weakest features | DDoS classification with Random Forest [57] |
| Backward Elimination | Stepwise feature removal based on performance | High-accuracy DDoS detection models [57] |
| Synthetic Minority Oversampling Technique (SMOTE) | Addressing class imbalance in datasets | LDDoS attack detection with imbalanced data [18] |
| Min-Max Scaler | Data normalization to uniform range | IoT network security data preprocessing [58] |
These research reagents form the foundation for implementing effective feature selection and hyperparameter tuning strategies. Each tool addresses specific challenges in the model optimization pipeline, from data preprocessing to final parameter adjustment. The selection of appropriate tools depends on the specific research domain, data characteristics, and computational constraints [58] [57] [18].
Technical Implementation Guide
Key Hyperparameters and Their Impact
Successful hyperparameter tuning requires understanding the function and optimal ranges for key parameters:
- Learning Rate: Determines step size during optimization; typically ranges from 0.0001 to 0.01. Too high causes overshooting, too low leads to slow convergence or local minima [63].
- Batch Size: Number of samples processed before updating parameters; small batches (32, 64) introduce noise but help avoid local minima, while large batches (128, 256) enable stable learning but require more memory [63].
- Number of Hidden Layers and Nodes: Determines model capacity; deeper networks learn complex patterns but risk overfitting. Generally start with 2-5 hidden layers, adjusting based on problem complexity [63].
- Dropout Ratio: Regularization technique to prevent overfitting; typically between 0.2-0.5. Higher values provide stronger regularization but limit learning capacity [63].
- Regularization Parameters: Control model complexity; L1 regularization creates sparsity (feature selection), while L2 regularization keeps weights small (improves stability). Values usually range from 0.001-0.1 [63].
Feature Selection Methodologies
Feature selection techniques generally fall into three categories:
- Filter Methods: Select features based on statistical measures (correlation, mutual information) independent of model performance. Efficient for high-dimensional datasets but may select redundant features [18].
- Wrapper Methods: Evaluate feature subsets based on model performance (e.g., Recursive Feature Elimination, Backward Elimination). More computationally intensive but typically yield better performance [57] [18].
- Embedded Methods: Perform feature selection as part of the model training process (e.g., Lasso regularization, tree-based importance). Balance efficiency and performance by incorporating selection into learning [58].
The experimental data and comparative analysis presented in this guide demonstrate the profound impact of systematic feature selection and hyperparameter tuning on model performance across diverse domains. For DoS detection accuracy benchmarking, the integration of Backward Elimination with Grid Search-optimized Random Forest currently represents the state-of-the-art, achieving 99.99% accuracy. In parallel, emerging nature-inspired optimization techniques like Coati-Grey Wolf Optimization and Improved Chaos African Vulture Optimization show significant promise for handling the complexity of modern IoT security challenges. The choice of optimization strategy must balance performance requirements with computational constraints, with Adaptive GridSearchCV offering an effective balance for many practical applications. As computational methods continue to evolve, the systematic integration of advanced feature selection and hyperparameter tuning will remain essential for developing accurate, robust, and deployable models in both cybersecurity and pharmaceutical research domains.
The adoption of artificial intelligence (AI) and machine learning (ML) models has transformed computational research, enabling unprecedented capabilities in pattern recognition and predictive modeling. However, this power often comes at the cost of understanding, as the most accurate models frequently operate as "black boxes" whose internal decision-making processes remain opaque [64]. This opacity presents critical challenges for researchers, scientists, and drug development professionals who require not just predictions but understandable, actionable insights that can inform scientific reasoning and experimental design.
The field of interpretable AI has emerged to bridge this gap, developing methods that help researchers understand how models arrive at their predictions. In the context of benchmarking computational methods, interpretability provides essential safeguards against embedded bias, enables model debugging, and helps researchers measure the effects of trade-offs in model architecture [64]. For drug development professionals, these capabilities are particularly valuable when predicting molecular interactions, assessing compound toxicity, or identifying promising drug candidates, as understanding model reasoning is essential for validating biologically plausible mechanisms [65].
This guide provides a comprehensive comparison of leading interpretability methods, evaluating their performance characteristics, implementation requirements, and suitability for different research contexts. By moving beyond black-box predictions, researchers can leverage AI not merely as a forecasting tool but as a collaborative partner in scientific discovery.
A Taxonomy of Interpretability Methods
Interpretability approaches can be broadly categorized into two distinct paradigms: intrinsic interpretability achieved through model design, and post-hoc interpretability obtained by applying explanation techniques after model training [66].
Intrinsically Interpretable Models
Intrinsically interpretable models are constrained in their architecture to ensure transparency in their decision-making processes. These include linear models, decision trees, decision rules, and their modern extensions [66]. The primary advantage of this approach is that the model itself is understandable - for example, the coefficients in a linear regression directly indicate feature importance, and a decision tree provides explicit decision paths. However, this interpretability often comes at the expense of predictive performance, particularly for complex, high-dimensional datasets where more sophisticated models typically achieve superior accuracy [64].
Post-hoc Interpretation Methods
Post-hoc methods separate interpretation from model training, applying explanation techniques after a model has been developed. This approach can be further divided into model-specific methods (which leverage internal model structures) and model-agnostic methods (which treat the model as a black box and analyze input-output relationships) [66]. Model-agnostic methods follow the SIPA principle: Sample from the data, perform an Intervention on the features, get Predictions from the model, and Aggregate the results to create explanations [66]. These methods provide flexibility but introduce an additional layer of approximation between the model and its explanation.
The following diagram illustrates the relationship between these interpretability approaches:
Comparative Analysis of Leading Interpretability Methods
The landscape of interpretability tools offers diverse approaches with distinct strengths and limitations. The following table compares five prominent methods across key characteristics:
| Method | Scope | Interpretation Type | Theoretical Foundation | Computational Demand | Stability |
|---|---|---|---|---|---|
| Partial Dependence Plots (PDP) | Global | Marginal feature effects | Statistical | Low | High |
| Permutation Feature Importance | Global | Feature ranking | Model performance | Medium | Medium |
| LIME (Local Interpretable Model-agnostic Explanations) | Local | Instance-level feature attribution | Local surrogate modeling | Medium | Low to Medium |
| SHAP (SHapley Additive exPlanations) | Local & Global | Instance-level feature contribution | Game theory | High | High |
| Global Surrogate | Global | Complete model approximation | Interpretable modeling | Medium | High |
Table 1: Comparison of key characteristics across interpretability methods
Performance Metrics and Benchmarking Results
Evaluating interpretability methods requires assessing multiple performance dimensions. The following quantitative comparison highlights trade-offs across critical metrics:
| Method | Explanation Fidelity | Representational Flexibility | Implementation Complexity | Human Understandability |
|---|---|---|---|---|
| PDP | Medium | Low | Low | High |
| Feature Importance | Medium | Low | Low | High |
| LIME | Medium | High | Medium | High |
| SHAP | High | Medium | High | Medium |
| Global Surrogate | Low to Medium | Medium | Medium | High |
Table 2: Performance assessment of interpretability methods across key metrics
Experimental Protocols for Method Evaluation
Benchmarking Framework Design
Robust evaluation of interpretability methods requires carefully designed experimental protocols that assess both technical performance and practical utility. The following workflow outlines a comprehensive benchmarking approach:
Implementation Guidelines for Key Methods
SHAP Implementation Protocol
SHAP (SHapley Additive exPlanations) grounds interpretability in game-theoretic principles, assigning each feature an importance value for a particular prediction. The implementation requires:
Background Data Selection: Choose a representative sample of training instances (typically 100-1000) to establish expected model behavior.
Explanation Generation:
- For tree-based models: Use TreeSHAP algorithm with polynomial time complexity
- For other model types: Employ KernelSHAP or LinearSHAP with appropriate feature perturbations
- Compute SHAP values for both individual predictions and global patterns
Result Interpretation:
- Analyze force plots for individual prediction explanations
- Generate summary plots to identify global feature importance
- Create dependence plots to reveal feature relationships
The mathematical foundation of SHAP derives from Shapley values, which fairly distribute the "payout" (prediction) among the "players" (features) according to their contribution across all possible subsets [64].
LIME Implementation Protocol
LIME (Local Interpretable Model-agnostic Explanations) creates local surrogate models to explain individual predictions:
Instance Perturbation:
- Generate synthetic dataset around instance to be explained
- For text data: remove words or phrases
- For tabular data: perturb features using normal distribution
- For image data: segment into superpixels and perturb segments
Surrogate Model Training:
- Weight perturbed instances by proximity to original instance
- Train interpretable model (linear regression, decision tree) on weighted dataset
- Use surrogate model to explain local behavior
Explanation Selection:
- Select top K features with highest weights in surrogate model
- Present explanation as feature-weight pairs or visual highlights
LIME's selective perturbation ensures that modifications are relevant to the local context, though the method can exhibit instability across different runs [67].
Application in Computational Research Domains
Drug Discovery and Development
Interpretability methods have proven particularly valuable in drug discovery, where understanding model reasoning is essential for validating biologically plausible mechanisms. Applications include:
- Target Identification: SHAP values reveal molecular features contributing to protein-ligand binding predictions, guiding medicinal chemistry optimization [65].
- Toxicity Prediction: LIME explanations identify structural alerts associated with compound toxicity, enabling early elimination of problematic candidates [65].
- Clinical Trial Optimization: Partial dependence plots model complex relationships between patient characteristics and treatment outcomes, supporting trial design decisions.
In credit scoring applications, SHAP has demonstrated particular utility by revealing how variables like income and credit history contribute to final credit decisions, providing transparency for regulatory compliance [67].
Cybersecurity Threat Detection
Interpretability methods play a crucial role in cybersecurity, where understanding detection models builds trust and enables improvement:
- Attack Classification: Feature importance analysis reveals network traffic characteristics most indicative of DDoS, DoS, and Mirai attacks [3].
- Model Validation: Permutation feature importance validates that detection models focus on semantically meaningful features rather than artifacts.
- Efficiency Optimization: Interpretable models like Decision Trees achieve 99.99% accuracy while reducing training time by 98.71% and prediction time by 99.53% compared to complex alternatives [3].
Successful implementation of interpretability methods requires both computational tools and conceptual frameworks. The following table outlines key resources for researchers:
| Resource Category | Specific Tools | Primary Function | Implementation Considerations |
|---|---|---|---|
| Interpretability Libraries | SHAP, LIME, Eli5, InterpretML | Method implementation | Python/R ecosystems, compatibility with ML frameworks |
| Visualization Tools | Matplotlib, Plotly, Seaborn | Explanation presentation | Customization capabilities, interactive features |
| Benchmarking Datasets | CICIoT2023, Bot-IoT, Clinical trial datasets | Method evaluation | Domain relevance, labeling quality, size |
| Model Training Frameworks | Scikit-learn, TensorFlow, PyTorch, XGBoost | Base model development | Integration with interpretability methods |
| Experimental Design | Cross-validation, A/B testing, Statistical tests | Validation framework | Rigor, reproducibility, domain appropriateness |
Table 3: Essential research resources for interpretable AI implementation
The choice of interpretability method depends fundamentally on the research context, balancing explanation needs against computational constraints. For global model understanding, Partial Dependence Plots and Permutation Feature Importance offer intuitive insights with minimal computational overhead. For explaining individual predictions, SHAP provides theoretically grounded, consistent attributions, while LIME offers flexibility in explanation representation.
In resource-constrained environments or applications requiring rapid iteration, simpler interpretable models like Decision Trees may provide the optimal balance between performance and transparency. As research in explainable AI continues to advance, the integration of interpretability into the model development lifecycle will become increasingly essential for building trustworthy, actionable AI systems across computational research domains.
The movement beyond black-box predictions represents not merely a technical challenge but a fundamental evolution in how researchers collaborate with AI systems - from passive consumers of predictions to active participants in a dialog with intelligence.
Rigorous Validation and Performance Comparison: Establishing a Platinum Standard
In computational methods research, the accuracy and reliability of a model are not determined by its performance on the data it was trained on, but by its ability to generalize to new, unseen data. External validation, the process of testing a predictive model on data sources that were not used during its development, is a critical step in successful model deployment [68]. Without rigorous external validation, models risk performance deterioration when applied to different healthcare facilities, geographic locations, or patient populations, as demonstrated by the widely implemented Epic Sepsis Model and various stroke risk scores in atrial fibrillation patients [68].
The transportability of predictive models across different data sources has gradually become a standard step in the life cycle of clinical prediction model development [68]. This is particularly crucial in drug development and materials science, where lack of rigorous reproducibility and validation are significant hurdles for scientific development [53]. In materials science, for instance, more than 70% of research works were shown to be non-reproducible, a number that could be much higher depending on the field of investigation [53].
Methodological Frameworks for External Validation
Statistical Estimation Methods
A novel method for estimating external model performance using only external summary statistics—without requiring access to patient-level external data—has shown promising results. This approach assigns weights to internal cohort units to reproduce a set of external statistics, then computes performance metrics using the labels and model predictions of the internal weighted units [68]. The method has demonstrated accurate estimations across multiple metrics, with 95th error percentiles for:
- Area under the receiver operating characteristics (AUROC): 0.03
- Calibration-in-the-large: 0.08
- Brier and scaled Brier scores: 0.0002 and 0.07, respectively [68]
This statistical approach allows evaluation of model performance on external sources even when unit-level data is inaccessible but statistical characteristics are available. Once obtained, these statistics can be repeatedly used to estimate the external performance of multiple models, considerably reducing the overhead of external validation [68].
Externally Controlled Trial Designs
In clinical research, externally augmented clinical trial (EACT) designs leverage external control data with patient-level information to contextualize single-arm studies. These designs use well-curated patient-level data for the standard of care treatment from one or more relevant data sources, allowing for adjustments of differences in pre-treatment covariates between enrolled patients and external data [69]. There are two primary EACT designs:
- ECA-SAT Design: A single-arm study combined with an external control arm (ECA) that serves as a comparator to evaluate the experimental treatment [69]
- Hybrid Randomized Design: Incorporates both internal randomization and external controls, potentially reducing overall sample size while maintaining randomization benefits [69]
These designs require high-quality patient-level records, rigorous methods, and validation analyses to effectively leverage external data while controlling for risks such as unmeasured confounders and data quality issues [69].
Table 1: Comparison of External Validation Approaches
| Validation Type | Data Requirements | Key Advantages | Limitations |
|---|---|---|---|
| Statistical Weighting Method [68] | Internal cohort data + external summary statistics | Does not require patient-level external data; reusable for multiple models | May fail if external statistics cannot be represented in internal cohort |
| External Control Arm (ECA) [69] | Individual patient data from external sources | Provides contextualized comparison for single-arm trials | Risk of bias from unmeasured confounders |
| Hybrid Randomized Design [69] | Combination of randomized controls and external data | Maintains benefits of randomization while improving efficiency | Complex implementation requiring careful statistical planning |
Benchmarking in Practice: Applications Across Disciplines
Healthcare and Clinical Prediction Models
A comprehensive benchmarking study evaluated the performance of a statistical weighting method across five large heterogeneous US data sources involving patients with pharmaceutically-treated depression. Models were trained to predict patients' risk of developing diarrhea, fracture, gastrointestinal hemorrhage, insomnia, or seizure [68]. The results demonstrated that:
- The upper quartile of AUROC estimation errors was usually below 0.02
- Values of internal-external AUROC difference were higher than estimation errors
- For the MDCR internal resource, the median estimation error was 0.011 (IQR 0.005-0.017), while the actual internal-external absolute difference was 0.027 (IQR 0.013-0.055) [68]
These findings confirm that internal validation significantly overestimates model performance compared to external testing, highlighting the critical importance of external validation sets.
Materials Science Informatics
The JARVIS-Leaderboard initiative provides an open-source, community-driven platform for benchmarking materials design methods across multiple categories: Artificial Intelligence (AI), Electronic Structure (ES), Force-fields (FF), Quantum Computation (QC), and Experiments (EXP) [53]. This comprehensive framework addresses several limitations of previous benchmarking efforts by:
- Providing flexibility to incorporate new tasks or benchmarks
- Accommodating multiple data modalities rather than specializing in a single modality
- Including both computational and experimental benchmarking
- Simplifying the process of user contributions to foster broader community engagement [53]
As of the most recent data, the platform contains 1281 contributions to 274 benchmarks using 152 methods with more than 8 million data points, continuously expanding [53].
Regulatory and Health Technology Assessment
A systematic literature review of analytical methods for comparing uncontrolled trials with external controls from real-world data revealed a significant methodological gap between state-of-the-art methods described in scientific literature and those used in actual regulatory and health technology assessment (HTA) submissions [70]. While scientific literature and guidelines recommend approaches similar to target trial emulation using advanced methods, external controls supporting regulatory and HTA decision making rarely align with this approach [70].
Table 2: Performance Metrics in External Validation Benchmarking
| Performance Metric | Purpose | Benchmark Performance [68] | Interpretation |
|---|---|---|---|
| Area Under ROC (AUROC) | Measures discrimination ability | 95th error percentile: 0.03 | Values closer to 1.0 indicate better discrimination |
| Calibration-in-the-large | Assesses overall calibration | 95th error percentile: 0.08 | Measures how well predicted probabilities match actual outcomes |
| Brier Score | Evaluates overall accuracy | 95th error percentile: 0.0002 | Lower values indicate better overall performance |
| Scaled Brier Score | Adjusted for overall accuracy | 95th error percentile: 0.07 | Accounts for baseline prevalence |
Experimental Protocols for External Validation
Statistical Weighting Protocol
The statistical weighting method for estimating external validation performance without patient-level external data follows a rigorous protocol [68]:
- Cohort Definition: Define a target cohort with specific inclusion/exclusion criteria
- Model Training: Train prediction models using internal data sources only
- External Statistics Extraction: Obtain population-level statistics from external cohorts
- Weight Optimization: Apply optimization algorithm to find weights for internal cohort units that induce weighted statistics similar to external statistics
- Performance Estimation: Compute performance metrics using the weighted internal units' labels and model predictions
The success of this weighting algorithm depends on the set of provided external statistics, requiring balance between feature inclusiveness and computational feasibility. The benchmark typically uses statistics of features with non-negligible model importance in each configuration [68].
Target Trial Emulation Framework
For externally controlled trials using real-world data, the target trial emulation framework provides a structured approach [70]:
- Protocol Development: A priori development of a detailed study protocol specifying all design elements
- Data Quality Assessment: Evaluation of real-world data sources for completeness, accuracy, and relevance
- Confounder Control: Application of appropriate statistical methods to control for measured confounding
- Sensitivity Analyses: Implementation of comprehensive sensitivity analyses to assess robustness of findings
- Transparency and Documentation: Complete documentation of all methodological choices and their rationale
This framework minimizes bias and increases trust in the results when using external controls [70].
Essential Research Reagents and Computational Tools
The following table details key resources for designing and implementing robust external validation studies:
Table 3: Research Reagent Solutions for External Validation Studies
| Resource Category | Specific Tools/Platforms | Function/Purpose | Application Context |
|---|---|---|---|
| Benchmarking Platforms | JARVIS-Leaderboard [53] | Integrated platform for benchmarking multiple computational methods | Materials science informatics |
| Statistical Methods | Weighting algorithms [68] | Estimate external performance without patient-level data | Healthcare prediction models |
| Data Harmonization | OHDSI tools [68] | Standardize data structure, content, and semantics across sources | Observational health research |
| Validation Frameworks | Target trial emulation [70] | Structured approach for using real-world data as external controls | Clinical trial design |
| Performance Metrics | AUROC, Calibration, Brier scores [68] | Quantitative assessment of model performance across domains | General predictive modeling |
Workflow Visualization
External Validation Workflow: This diagram illustrates the comprehensive process for designing robust external validation studies, highlighting the critical transition from internal development to external testing.
Robust validation studies incorporating external test sets are essential for verifying the transportability and real-world performance of predictive models across computational research domains. The statistical and methodological frameworks presented provide researchers with structured approaches for implementing external validation, whether through direct testing on external datasets or through innovative methods that estimate performance using summary statistics. As benchmarking initiatives like JARVIS-Leaderboard demonstrate, community-driven platforms with standardized evaluation protocols are accelerating scientific development by enhancing reproducibility, transparency, and methodological rigor across fields. For regulatory applications and clinical decision-making, the adoption of target trial emulation frameworks and state-of-the-art analytical methods for external controls will be crucial for generating reliable evidence from real-world data sources.
Benchmarking the accuracy of Density of States (DOS) predictions is a critical endeavor in computational materials science, with profound implications for accelerating the discovery of new materials, including those for pharmaceutical applications. The DOS, which quantifies the distribution of available electronic states at each energy level, underlies fundamental optoelectronic properties and is highly relevant for understanding material behavior in various environments [71]. As the field moves from highly specialized models toward universal machine-learning potentials, the need for standardized performance metrics and rigorous benchmarking protocols has become increasingly important. This guide provides a comparative analysis of contemporary computational methods for predicting the DOS, focusing on their predictive accuracy and computational efficiency. It is designed to equip researchers and drug development professionals with the data and context needed to select appropriate models for their specific research objectives, ultimately contributing to the accelerated design of novel materials.
Comparative Performance Analysis of DOS Methods
The following table summarizes the key performance metrics of several prominent machine learning models for DOS prediction, as evaluated on standardized benchmarks.
Table 1: Performance Comparison of Selected DOS Prediction Models
| Model Name | Core Architecture | Primary Dataset | Key Performance Metric | Reported Performance | Computational Note |
|---|---|---|---|---|---|
| DOSnet [72] | Convolutional Neural Network (CNN) | Custom dataset (37,000 adsorption energies on bimetallic surfaces) | Mean Absolute Error (MAE) for adsorption energy prediction | ~0.138 eV (weighted average MAE) | Leverages DOS for property prediction; good compromise on training cost. |
| PET-MAD-DOS [71] | Point Edge Transformer (PET) | Massive Atomistic Diversity (MAD) dataset | Integrated Absolute Error (IAE) on external datasets (e.g., MD22, SPICE) | ~0.15-0.20 IAE (on molecular datasets) | Universal model; demonstrates semi-quantitative agreement across diverse systems. |
| Bespoke PET Models [71] | Point Edge Transformer (PET) | System-specific datasets (e.g., GaAs, LiPS, HEA) | Integrated Absolute Error (IAE) | ~50% lower error than universal PET-MAD-DOS | Higher accuracy for specific systems but lacks generalizability. |
Experimental Protocols for Benchmarking
To ensure the reproducibility and fair comparison of results, the studies cited herein adhere to rigorous experimental protocols. This section outlines the common methodologies for training, evaluating, and validating DOS prediction models.
Data Sourcing and Preprocessing
A critical first step is the curation and preparation of datasets. The Massive Atomistic Diversity (MAD) dataset, for instance, is a compact yet highly diverse collection used for training universal models like PET-MAD-DOS. It includes multiple subsets: 3D and 2D crystals (MC3D, MC2D), rattled and randomized structures to probe stability, and molecular crystals/fragments (SHIFTML) [71]. For external validation, models are often tested on publicly available datasets such as MPtrj (relaxation trajectories), Matbench (inorganic crystals), SPICE (drug-like molecules), and MD22 (biomolecular trajectories) [71]. These external datasets are typically recomputed using consistent Density Functional Theory (DFT) settings to maintain comparability with training data. Preprocessing of the DOS itself may involve downsampling to a standard energy resolution (e.g., 0.01 eV) and orbital-projection for the input features [72].
Model Training and Evaluation Metrics
Models are typically trained in a supervised learning framework, using DFT-calculated DOS as the ground truth. The PET-MAD-DOS model, for example, employs a transformer-based architecture that does not enforce rotational constraints but learns equivariance through data augmentation [71]. A standard practice is to perform k-fold cross-validation (e.g., fivefold) to ensure robust performance estimation and mitigate overfitting [72].
The primary metric for evaluating the quality of the predicted DOS is the Integrated Absolute Error (IAE), which measures the absolute difference between the predicted and true DOS over the energy range of interest [71]. For downstream tasks, such as predicting catalytic properties, the Mean Absolute Error (MAE) of the derived property (e.g., adsorption energy) is a more application-relevant metric, often reported in electronvolts (eV) [72]. Performance is evaluated not only on a held-out test set from the training data but, crucially, on external datasets to assess the model's generalizability to unseen chemical spaces [71].
Workflow Diagram for DOS Benchmarking
The following diagram illustrates the logical workflow and key decision points involved in benchmarking machine learning models for DOS prediction, from data preparation to final model selection.
The Scientist's Toolkit: Essential Research Reagents
The following table details key computational tools and datasets that function as essential "research reagents" in the field of machine learning for DOS prediction.
Table 2: Essential Research Reagents for DOS Machine Learning
| Tool / Resource | Type | Primary Function | Relevance to Drug Development |
|---|---|---|---|
| MAD Dataset [71] | Dataset | A compact, diverse training set for universal models, encompassing molecules, surfaces, and bulk crystals. | Provides a foundational model that can be fine-tuned for specific molecular systems of pharmaceutical interest. |
| PET Architecture [71] | Model Architecture | A transformer-based graph neural network for modeling atomic systems without explicit rotational constraints. | Enables accurate property prediction for complex, flexible drug molecules and their interactions with surfaces. |
| DOSnet [72] | Specialized Model | A CNN-based model that automatically extracts features from the DOS to predict surface adsorption energies. | Useful for screening catalytic materials for synthesizing pharmaceutical compounds or modeling drug-surface interactions. |
| CIC-DDoS2019 [13] | Benchmark Dataset | A comprehensive dataset of network traffic used for evaluating intrusion detection systems (Note: Contextual for cybersecurity, included for completeness). | While not directly related, it exemplifies the type of standardized benchmark needed for fair comparison of models in any domain. |
| SHAP/LIME [73] | Analysis Tool | Explainable AI (XAI) techniques for interpreting the predictions of complex machine learning models. | Critical for building trust in model predictions and understanding the atomic-level features that drive DOS outcomes in molecular systems. |
The benchmarking of DOS prediction methods reveals a dynamic landscape where the trade-off between generalizability and specialized accuracy is a central theme. Universal models like PET-MAD-DOS represent a significant advancement, offering semi-quantitative accuracy across a vast chemical space with linear scaling, making them highly computationally efficient for exploratory research and large-scale screening [71]. In contrast, specialized models, including DOSnet and bespoke system-specific models, can achieve higher accuracy for well-defined problems, with bespoke models demonstrating up to 50% lower error on their target systems [72] [71]. The choice of model ultimately depends on the research goal: universal models are ideal for scanning vast chemical spaces and generating initial leads, while specialized models are preferable for obtaining high-fidelity results on a specific class of materials, a common scenario in targeted drug development projects. As the field progresses, the integration of explainable AI and standardized benchmarking protocols will be crucial for advancing the reliability and adoption of these powerful computational tools.
Software benchmarking provides a critical framework for evaluating computational methods across diverse scientific disciplines, enabling objective performance comparisons and supporting data-driven decision-making. In computational research, robust benchmarking methodologies are essential for validating novel algorithms, optimizing resource allocation, and establishing performance baselines against existing solutions. This comparative analysis examines software benchmarking applications across two distinct domains—IoT security and pharmaceutical development—to elucidate common principles, methodological considerations, and performance metrics that transcend disciplinary boundaries. By synthesizing benchmarking approaches from these fields, this guide establishes a foundational understanding of how systematic performance evaluation enhances research reproducibility, accelerates innovation, and improves predictive accuracy in computational methodologies.
Case Study I: Benchmarking Machine Learning Models for IoT Attack Classification
Experimental Framework and Dataset
A comprehensive benchmarking study evaluated five supervised machine learning algorithms for classifying Denial of Service (DoS), Distributed Denial of Service (DDoS), and Mirai attacks in IoT environments using the CICIoT2023 dataset [3]. The research addressed critical methodological challenges including class imbalance through undersampling techniques and implemented three distinct feature selection approaches: Chi-square, Principal Component Analysis (PCA), and Random Forest Regressor (RFR) [3]. The benchmarking protocol incorporated multiple performance dimensions, assessing not only classification accuracy but also computational efficiency through training and prediction times, providing a holistic evaluation framework for resource-constrained IoT environments [3].
Performance Metrics and Results
The benchmarking results demonstrated that the Random Forest Regressor (RFR) feature selection method consistently outperformed other approaches across multiple evaluation criteria [3]. As detailed in Table 1, three algorithms—Random Forest, Decision Tree, and Gradient Boosting—achieved perfect 99.99% accuracy when paired with RFR feature selection, highlighting the critical importance of feature engineering in classification performance [3].
Table 1: Performance Comparison of Machine Learning Algorithms with RFR Feature Selection
| Algorithm | Accuracy (%) | Precision (%) | Recall (%) | F1-Score (%) | Training Time Reduction (%) | Prediction Time Reduction (%) |
|---|---|---|---|---|---|---|
| Random Forest | 99.99 | 99.98 | 99.99 | 99.99 | 96.45 | 98.22 |
| Decision Tree | 99.99 | 99.99 | 99.98 | 99.99 | 98.71 | 99.53 |
| Gradient Boosting | 99.99 | 99.97 | 99.98 | 99.98 | 95.83 | 97.91 |
| K-Nearest Neighbors | 99.12 | 98.95 | 98.87 | 98.91 | 92.17 | 94.36 |
| Naive Bayes | 97.85 | 97.42 | 97.18 | 97.30 | 89.24 | 92.05 |
Beyond accuracy metrics, the benchmarking revealed substantial improvements in computational efficiency. The Decision Tree model achieved a 98.71% reduction in training time and a 99.53% reduction in prediction time compared to previously reported results, demonstrating that optimized algorithms can deliver both superior accuracy and enhanced computational efficiency [3]. The study also identified specific classification challenges, particularly in distinguishing between DoS and DDoS attacks due to their shared network characteristics, while Mirai attacks were more readily distinguishable based on their distinct operational patterns [3].
Experimental Protocol
The benchmarking methodology followed a structured workflow encompassing data preprocessing, feature selection, model training, and comprehensive evaluation. The following diagram illustrates the complete experimental protocol:
Diagram 1: IoT Security Benchmarking Workflow
Case Study II: Benchmarking Deep Learning Architectures for DDoS Detection in Software-Defined Networking
Hybrid Deep Learning Framework
A separate benchmarking initiative evaluated six deep learning models for DDoS attack classification in Software-Defined Networking (SDN) environments, including Multilayer Perceptron (MLP), one-dimensional Convolutional Neural Network (1D-CNN), Long Short-Term Memory (LSTM), Gated Recurrent Unit (GRU), Recurrent Neural Network (RNN), and a novel hybrid CNN-GRU architecture [74]. The experimental protocol addressed class imbalance through Synthetic Minority Over-sampling Technique (SMOTE), creating a balanced dataset of 24,500 samples (12,250 benign and 12,250 attacks) [74]. The benchmarking framework incorporated a comprehensive preprocessing pipeline with missing value verification, feature normalization using StandardScaler, data reshaping into 3D format for temporal models, and stratified train-test split (80% training, 20% testing) to maintain representative class distributions [74].
Classification Performance and Generalization
The hybrid CNN-GRU model demonstrated perfect classification performance, achieving 100% accuracy, 1.0000 precision, recall, F1-score, and ROC AUC on test data [74]. As shown in Table 2, the model also exhibited exceptional generalization capability during cross-validation, achieving a mean accuracy of 99.70% (±0.09%) and perfect AUC of 1.0000 (±0.0000) across 5-fold stratified cross-validation [74].
Table 2: Deep Learning Model Performance for DDoS Classification
| Model Architecture | Test Accuracy (%) | Precision | Recall | F1-Score | Cross-Validation Accuracy (%) | AUC |
|---|---|---|---|---|---|---|
| CNN-GRU (Hybrid) | 100.00 | 1.0000 | 1.0000 | 1.0000 | 99.70 ± 0.09 | 1.0000 |
| GRU | 99.92 | 0.9990 | 0.9989 | 0.9990 | 99.25 ± 0.15 | 0.9998 |
| 1D-CNN | 99.88 | 0.9985 | 0.9984 | 0.9985 | 99.18 ± 0.18 | 0.9996 |
| LSTM | 99.85 | 0.9982 | 0.9980 | 0.9981 | 99.12 ± 0.21 | 0.9994 |
| MLP | 99.45 | 0.9940 | 0.9938 | 0.9939 | 98.75 ± 0.24 | 0.9982 |
| RNN | 99.25 | 0.9918 | 0.9915 | 0.9916 | 98.45 ± 0.31 | 0.9975 |
The superior performance of the CNN-GRU hybrid architecture stems from its synergistic combination of convolutional layers for spatial pattern extraction and GRU layers for temporal sequence learning [74]. This architectural integration proved particularly effective for analyzing network traffic data, which contains both spatial features (packet size distributions, flow durations) and temporal dependencies (connection patterns over time) [74].
Experimental Methodology
The benchmarking methodology for evaluating deep learning architectures followed a structured protocol with distinct phases, as illustrated below:
Diagram 2: Deep Learning Benchmarking Protocol for DDoS Detection
Case Study III: Benchmarking in Pharmaceutical Development
Dynamic Benchmarking for Clinical Success Prediction
The pharmaceutical industry employs sophisticated benchmarking methodologies to assess drug development success probabilities, with traditional approaches relying on historical analysis of phase transition success rates [75]. Legacy benchmarking solutions typically calculate Probability of Success (POS) by multiplying phase transition rates, often resulting in risk underestimation and overly optimistic projections [75]. These conventional approaches face significant limitations including infrequent data updates, high-level unstructured data, inadequate aggregation methods limiting advanced filtering, and simplistic analytical methodologies [75].
Next-generation dynamic benchmarking platforms address these limitations through real-time data integration, expertly curated historical data extending back decades, advanced aggregation accommodating non-standard development paths, flexible filtering based on proprietary ontologies, and refined methodologies that account for diverse development trajectories [75]. These platforms enable more accurate POS assessments by incorporating multidimensional filters including modality, mechanism of action, disease severity, line of treatment, adjuvant status, biomarker presence, and population characteristics [75].
Benchmarking Applications in Computational Biology
In computational biology, benchmarking platforms facilitate rigorous evaluation of gene expression forecasting methods [76]. The benchmarking framework combines a panel of 11 large-scale perturbation datasets with an expression forecasting software engine that interfaces with diverse computational methods [76]. This systematic approach enables objective comparison of algorithm performance, parameter configurations, and auxiliary data sources, revealing that expression forecasting methods frequently fail to outperform simple baseline models [76]. Such benchmarking initiatives provide critical resources for method improvement and identify specific contexts where expression forecasting demonstrates practical utility [76].
Table 3: Pharmaceutical Benchmarking Methodologies Comparison
| Benchmarking Aspect | Traditional Approach | Dynamic Benchmarking | Advantages |
|---|---|---|---|
| Data Currency | Infrequent updates (quarterly/annually) | Real-time data incorporation | Reflects most recent clinical outcomes |
| Data Structure | High-level, unstructured data | Expertly curated, structured data | Enables precise therapeutic area analysis |
| Development Paths | Standard phase progression assumed | Accommodates skipped/dual phases | Adapts to innovative trial designs |
| Filtering Capabilities | Limited dimensional filtering | Multi-dimensional ontology-based filtering | Customized analysis for specific treatment settings |
| POS Methodology | Simple phase transition multiplication | Nuanced path-by-path and phase-by-phase analysis | More accurate risk assessment |
Cross-Domain Comparative Analysis of Benchmarking Methodologies
Common Methodological Principles
Despite application-specific differences, effective benchmarking methodologies across domains share fundamental principles: comprehensive data preprocessing, appropriate handling of class imbalances, multi-dimensional performance assessment, and rigorous validation protocols. The examined case studies consistently demonstrate that superior benchmarking outcomes require attention to data quality, appropriate algorithm selection, and consideration of computational efficiency alongside accuracy metrics [3] [74] [75].
In IoT security benchmarking, computational efficiency emerges as a critical metric alongside accuracy, particularly for resource-constrained environments [3]. Similarly, pharmaceutical benchmarking emphasizes the importance of real-time data incorporation and multidimensional filtering to enhance predictive accuracy [75]. These commonalities highlight the universal importance of designing benchmarking frameworks that address both technical performance and practical implementation constraints.
Domain-Specific Benchmarking Adaptations
Each domain requires specialized adaptations to address unique challenges. IoT security benchmarking incorporates specific attack typologies (DoS, DDoS, Mirai) and employs feature selection methods optimized for network traffic data [3]. Pharmaceutical development benchmarking utilizes specialized ontologies and filtering mechanisms tailored to biological concepts and clinical trial parameters [75]. Deep learning benchmarking for network security employs temporal data reshaping and architectural innovations specifically designed to capture spatial and temporal patterns in network traffic [74].
The following diagram illustrates the conceptual relationships between shared benchmarking principles and domain-specific adaptations:
Diagram 3: Benchmarking Principles and Domain Adaptations
The Scientist's Toolkit for Software Benchmarking
Effective benchmarking across computational domains requires specialized "research reagents"—standardized datasets, algorithmic frameworks, and evaluation metrics that enable reproducible performance assessment. Table 4 details essential resources referenced in the case studies:
Table 4: Essential Research Reagents for Computational Benchmarking
| Resource Category | Specific Resource | Application Domain | Function and Purpose |
|---|---|---|---|
| Reference Datasets | CICIoT2023 | IoT Security | Provides labeled network traffic data for training and evaluating attack classification models [3] |
| Reference Datasets | SDN Traffic Dataset | Network Security | Enables binary classification of network traffic into benign or attack classes in SDN environments [74] |
| Reference Datasets | Clinical Trial Histories | Pharmaceutical Development | Offers historical drug development data for probability of success calculations and risk assessment [75] |
| Data Processing Tools | SMOTE | Multiple Domains | Addresses class imbalance through synthetic minority oversampling to prevent model bias [74] |
| Data Processing Tools | StandardScaler | Multiple Domains | Normalizes numerical features to standardize value distributions and improve algorithm convergence [74] |
| Feature Selection Methods | Random Forest Regressor | IoT Security | Identifies most predictive features for attack classification, enhancing model accuracy and efficiency [3] |
| Feature Selection Methods | Chi-square, PCA | IoT Security | Provides alternative feature selection approaches for comparative performance assessment [3] |
| Algorithmic Frameworks | Hybrid CNN-GRU | Network Security | Combines spatial pattern extraction and temporal sequence learning for enhanced detection accuracy [74] |
| Algorithmic Frameworks | Random Forest, Decision Tree | IoT Security | Offers interpretable machine learning models with high accuracy and computational efficiency [3] |
| Evaluation Metrics | Accuracy, Precision, Recall, F1 | Multiple Domains | Provides standard classification performance assessment across domains [3] [74] |
| Evaluation Metrics | Training/Prediction Time | Resource-Constrained Environments | Measures computational efficiency for practical deployment considerations [3] |
| Evaluation Metrics | ROC AUC | Multiple Domains | Assesses model discrimination capability across classification thresholds [74] |
This comparative analysis demonstrates that rigorous software benchmarking methodologies provide essential foundations for advancing computational research across diverse domains. The examined case studies reveal common principles underlying effective benchmarking frameworks, including comprehensive data preprocessing, multidimensional performance assessment, and robust validation protocols. Domain-specific adaptations address unique challenges in IoT security, pharmaceutical development, and network protection, yet share fundamental methodological approaches. As computational methods continue to evolve, standardized benchmarking practices will play an increasingly critical role in validating algorithmic performance, guiding resource allocation, and establishing reproducible baselines for comparative analysis. The research reagents and methodological frameworks detailed in this analysis provide practical resources for researchers developing and evaluating computational methods across scientific disciplines.
In computational drug discovery, achieving high statistical performance on benchmark datasets is a common goal, yet it is an insufficient indicator of real-world success. The ultimate test for any computational method lies in its ability to predict biologically meaningful outcomes that translate to experimental validation and therapeutic applications. This review moves beyond mere statistical agreement to evaluate the biological relevance of several prominent computational methods. We focus on their performance in predicting critical biological phenomena, including protein-ligand interactions, intrinsically disordered protein (IDP) behavior, and complex system properties, by examining their validation through experimental protocols. This analysis is framed within a broader thesis on benchmarking the true accuracy of computational methods across the drug discovery pipeline, providing researchers with a pragmatic assessment of each method's utility in biologically complex scenarios.
Comparative Analysis of Computational Methods
The following table summarizes the core methodologies, key biological applications, and the nature of experimental validation for the computational approaches discussed in this review.
Table 1: Comparison of Computational Methods and Their Biological Evaluation
| Computational Method | Key Biological Application | Typical Experimental Validation | Reported Strengths | Reported Limitations |
|---|---|---|---|---|
| Molecular Docking & Structure-Based Virtual Screening [16] [17] [77] | Predicting protein-ligand binding modes and affinities; identifying potential drug candidates from ultra-large libraries (billions of compounds). | Affinity selection–mass spectrometry (AS-MS); DNA-encoded library (DEL) selection; functional cell-based assays; crystallography for binding mode confirmation [16] [17]. | Success in identifying sub-nanomolar ligands for targets like GPCRs and kinases; direct structural insights [16]. | Accuracy depends on receptor structure quality; can struggle with protein flexibility, especially in IDPs [78] [17]. |
| Quantitative Structure-Activity Relationship (QSAR) [17] [77] | Establishing mathematical relationships between chemical structure and biological activity for lead optimization. | In vitro potency and selectivity assays (e.g., IC50 determination); in vivo efficacy studies [17]. | High-throughput; useful for optimizing pharmacophores and predicting ADMET properties [77]. | Reliant on high-quality, congeneric training data; may lack mechanistic interpretability. |
| Machine Learning (ML) & Deep Learning (DL) for Ligand Properties [16] [17] | Predicting target activities and physicochemical properties in lieu of 3D structure; generative molecular design. | Experimental validation of top-ranked AI-generated compounds in biochemical and cellular assays [16]. | Rapid identification of novel chemotypes; can leverage large chemical databases [16]. | "Black box" nature; risk of learning dataset biases instead of underlying biology. |
| Biomolecular Simulations (MD, QM/MM) [17] | Elucidating drug action mechanisms, identifying allosteric sites, and studying protein dynamics. | Spectroscopic methods (e.g., NMR); site-directed mutagenesis; calculation of binding free energies [17]. | Provides atomic-level detail and time-resolved insights into mechanisms [17]. | Computationally expensive; limited by timescales and force field accuracy. |
| Ensemble & Transformer-based IDP Prediction [78] | Predicting intrinsically disordered regions (IDRs) and their functions (e.g., signaling, molecular recognition). | Nuclear Magnetic Resonance (NMR) spectroscopy; cross-linking coupled with mass spectrometry [78]. | Capable of handling proteins lacking fixed 3D structure; insights into PTMs and interactomes [78]. | Validation remains challenging due to the dynamic nature of IDPs. |
Experimental Protocols for Biological Validation
Experimental Validation of Virtual Screening Hits
The transition from in silico prediction to experimental validation is critical. For hits identified from virtual screening of ultra-large libraries, the process typically involves several stages [16]:
- Ligand Synthesis & Characterization: Top-ranking computational hits are synthesized, and their purity is confirmed using analytical techniques like liquid chromatography-mass spectrometry (LC-MS).
- Biochemical Affinity Assays: Techniques like Affinity Selection–Mass Spectrometry (AS-MS) are employed. In AS-MS, a mixture of compounds is incubated with the target protein, and unbound molecules are separated. The protein-ligand complex is then denatured, and the bound ligands are identified via MS, providing direct evidence of binding [16].
- Functional Activity Assays: The potency of confirmed binders is measured using assays specific to the target's function (e.g., enzyme inhibition assays, cell-based reporter assays for GPCRs) to determine half-maximal inhibitory concentration (IC50) or effective concentration (EC50) values.
- Structural Validation: The binding mode predicted by docking is often confirmed experimentally using X-ray crystallography or cryo-electron microscopy (cryo-EM) by solving the structure of the protein-ligand complex [16].
Characterization of Intrinsically Disordered Proteins
Intrinsically disordered proteins (IDPs) and regions (IDRs) challenge conventional structural biology methods. Experimental validation for computational predictions of IDPs relies on techniques that capture dynamic states [78]:
- Nuclear Magnetic Resonance (NMR) Spectroscopy: NMR chemical shifts are highly sensitive to secondary structure. IDPs exhibit characteristic chemical shifts that distinguish them from folded proteins, allowing residue-level identification of disordered regions.
- Cross-linking Mass Spectrometry (XL-MS): Cross-linkers covalently bind proximal amino acids, even in flexible regions. Analyzing these cross-linked peptides by MS provides low-resolution structural restraints and interaction information for IDPs within complexes.
- Small-Angle X-Ray Scattering (SAXS): SAXS provides information about the overall size, shape, and flexibility of proteins in solution, yielding ensemble-averaged parameters that are characteristic of disordered states.
The following workflow diagram illustrates the integrated computational and experimental pipeline for validating predictions of ordered and disordered protein-ligand interactions.
Diagram 1: Integrated Computational-Experimental Validation Workflow.
The Scientist's Toolkit: Essential Research Reagents and Materials
Successful biological validation relies on a suite of specialized reagents and tools. The table below details key materials used in the experimental protocols cited in this review.
Table 2: Essential Research Reagents for Experimental Validation
| Reagent / Material | Function in Validation | Key Application Example |
|---|---|---|
| Target Protein (Purified) | The macromolecule of interest (e.g., kinase, GPCR, enzyme) used in binding and activity assays. | Essential for all in vitro assays, including AS-MS, biochemical activity assays, and structural studies (crystallography, Cryo-EM) [16] [17]. |
| Chemical Library / DNA-Encoded Library (DEL) | A diverse collection of small molecules used for screening and identifying initial hit compounds. | Used in virtual screening follow-up and direct experimental screening (e.g., DEL selection) to find binders [16]. |
| Affinity Selection Mass Spectrometry (AS-MS) Platform | A technology that physically separates protein-bound ligands from unbound ones and identifies binders via mass spectrometry. | Validates hits from virtual screening by confirming direct binding to the purified target protein [16]. |
| Stable Isotope-Labeled Proteins (e.g., 15N, 13C) | Proteins produced with stable isotopes for analysis by NMR spectroscopy. | Allows residue-level characterization of protein structure and dynamics, crucial for validating IDP/IDR predictions [78]. |
| Cross-linking Reagents (e.g., DSS, BS3) | Chemicals that form covalent bonds between proximate amino acids in proteins or protein complexes. | Used in XL-MS to provide experimental distance restraints for IDP conformational ensembles and protein interaction networks [78]. |
| Cell-Based Reporter Assay Systems | Engineered cell lines containing a reporter gene (e.g., luciferase) activated by a specific biological pathway. | Tests the functional biological activity and cellular efficacy of predicted compounds (e.g., for GPCR targets) [16]. |
The computational methods reviewed herein demonstrate a growing capacity to generate predictions with significant biological relevance. Methods like molecular docking and deep learning have shown concrete success in identifying potent, target-selective ligands that are subsequently validated experimentally. Simultaneously, emerging techniques for IDP prediction are beginning to grapple with the complexity of proteins that defy classical structure-function paradigms. The critical differentiator for a method's practical value is its integration with robust experimental protocols—from AS-MS and DEL for binding confirmation to NMR and XL-MS for characterizing disorder. As the field progresses, the focus must remain on this cycle of computational prediction and biological validation, ensuring that statistical benchmarks are firmly grounded in real-world biological meaning.
Conclusion
Effective benchmarking is the cornerstone of reliable computational drug discovery, transforming abstract predictions into trusted tools for decision-making. The key takeaways underscore the necessity of using standardized frameworks, rigorous external validation, and transparent methodologies to assess accuracy across diverse computational approaches. Future progress hinges on the development of more comprehensive 'platinum standard' benchmarks, particularly for complex targets like disordered proteins and beyond-Rule-of-5 molecules. The integration of advanced AI with high-fidelity physical models and the establishment of universally accepted reporting standards will be crucial for accelerating the translation of computational discoveries into successful clinical outcomes, ultimately building a more predictive and efficient drug development pipeline.
References
- 1. Essential guidelines for computational method benchmarking [https://pmc.ncbi.nlm.nih.gov/articles/PMC6584985/]
- 2. Genomic reproducibility in the bioinformatics era [https://genomebiology.biomedcentral.com/articles/10.1186/s13059-024-03343-2]
- 3. Evaluating machine learning approaches for multiple ... [https://www.nature.com/articles/s41598-025-23711-7]
- 4. Understanding Benchmarking Analysis: A Step-by- ... [https://www.comparables.ai/articles/understanding-benchmarking-analysis-step-by-step-guide]
- 5. DDoS attack detection using CNN-BiLSTM with attention ... [https://www.sciencedirect.com/science/article/pii/S277250302500026X]
- 6. Designing Effective Data Visualizations [https://guides.library.jhu.edu/datavisualization/design]
- 7. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 8. Efficiency of different measures for defining the applicability ... [https://jcheminf.biomedcentral.com/articles/10.1186/s13321-017-0230-2]
- 9. Benchmarking community drug response prediction models [https://arxiv.org/html/2503.14356v1]
- 10. Comparative analysis of deep learning and traditional ... [https://www.nature.com/articles/s41598-025-16553-w]
- 11. Distributed denial-of-service (DDOS) attack detection using ... [https://www.nature.com/articles/s41598-024-84879-y]
- 12. Binary classification of Low-Rate DoS attacks using Long ... [https://www.sciencedirect.com/science/article/pii/S2215098625001041]
- 13. Comparative analysis of deep learning models for effective ... [https://jesit.springeropen.com/articles/10.1186/s43067-025-00267-0]
- 14. A comparative study of machine learning and deep ... [https://www.sciencedirect.com/science/article/pii/S2590005625000335]
- 15. Benchmarking Dataset - an overview | ScienceDirect Topics [https://www.sciencedirect.com/topics/computer-science/benchmarking-dataset]
- 16. Computational approaches streamlining drug discovery [https://www.nature.com/articles/s41586-023-05905-z]
- 17. A Review on Applications of Computational Methods in Drug ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7144386/]
- 18. Optimizing feature selection and deep learning techniques ... [https://link.springer.com/article/10.1007/s43926-025-00182-w]
- 19. Amazon introduces two benchmark datasets for evaluating ... [https://aws.amazon.com/blogs/devops/amazon-introduces-two-benchmark-datasets-for-evaluating-ai-agents-ability-on-code-migration/]
- 20. An Introduction to LLM Benchmarking [https://www.confident-ai.com/blog/the-current-state-of-benchmarking-llms]
- 21. Computational approaches to DMPK: A realistic ... [https://www.sciencedirect.com/science/article/pii/S1359644625001357]
- 22. Proton affinity Revisited: Benchmarking computational ... [https://www.sciencedirect.com/science/article/abs/pii/S2210271X24000161]
- 23. Analytical benchmark problems and methodological ... [https://link.springer.com/article/10.1007/s11831-025-10392-8]
- 24. Color Palette - University Branding and Identity Guidelines [https://identity.unc.edu/brand/color-palette/]
- 25. A review of quantitative structure-activity relationship [https://www.sciencedirect.com/science/article/abs/pii/S0169743924002181]
- 26. A (Comprehensive) Review of the Application ... [https://www.mdpi.com/2076-3417/15/3/1206]
- 27. QSAR Toolbox [https://qsartoolbox.org/]
- 28. OECD QSAR Toolbox [https://www.oecd.org/en/data/tools/oecd-qsar-toolbox.html]
- 29. Sciome to Spotlight Breakthroughs in Read-Across and ... [https://www.sciome.com/sciome-to-spotlight-breakthroughs-in-read-across-and-qsar-at-ascct-2025/]
- 30. Topological regression as an interpretable and efficient ... [https://www.nature.com/articles/s41467-024-49372-0]
- 31. Benchmarking the Structure-Based Virtual Screening ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12363558/]
- 32. Pairwise Performance Comparison of Docking Scoring ... [https://www.mdpi.com/1420-3049/30/13/2777]
- 33. A database for large-scale docking and experimental results [https://pmc.ncbi.nlm.nih.gov/articles/PMC11888352/]
- 34. Essential guidelines for computational method benchmarking [https://genomebiology.biomedcentral.com/articles/10.1186/s13059-019-1738-8]
- 35. Docking Benchmark Group - TDC [https://tdcommons.ai/benchmark/docking_group/overview/]
- 36. A comprehensive survey of scoring functions for protein ... [https://bmcbioinformatics.biomedcentral.com/articles/10.1186/s12859-024-05991-4]
- 37. DeepTarget predicts anti-cancer mechanisms of action ... [https://www.nature.com/articles/s41698-025-01111-4]
- 38. Computational deep dive surfaces unexplored world of ... [https://sbpdiscovery.org/press/computational-deep-dive-surfaces-unexplored-world-of-cancer-drug-targets/]
- 39. DeepTarget tool helps identify secondary cancer drug targets [https://www.drugtargetreview.com/news/190717/deeptarget-tool-helps-identify-secondary-cancer-drug-targets/]
- 40. New Computational Tool Shows Strong Accuracy in ... [https://ascopost.com/news/november-2025/new-computational-tool-shows-strong-accuracy-in-predicting-cancer-drug-targets]
- 41. Extending quantum-mechanical benchmark accuracy to ... [https://www.nature.com/articles/s41467-025-63587-9]
- 42. Resolving data bias improves generalization in binding ... [https://www.nature.com/articles/s42256-025-01124-5]
- 43. Binding affinity predictions with hybrid quantum-classical ... [https://www.nature.com/articles/s41598-023-45269-y]
- 44. Quantum Resources Required for Binding Affinity ... [https://arxiv.org/html/2406.18744v1]
- 45. Comprehensive benchmarking of computational tools for ... [https://jcheminf.biomedcentral.com/articles/10.1186/s13321-024-00931-z]
- 46. For drug discovery, QSAR and molecular descriptors are ... [https://www.linkedin.com/pulse/drug-discovery-qsar-molecular-descriptors-more-relevant-vijay-masand-vdycf]
- 47. Benchmarking 2D/3D/MD-QSAR Models for Imatinib ... [https://pubmed.ncbi.nlm.nih.gov/32623886/]
- 48. Free and open-source QSAR-ready workflow for automated ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10880251/]
- 49. Benchmarking compound activity prediction for real-world ... [https://www.nature.com/articles/s42004-024-01204-4]
- 50. Strategies for robust, accurate, and generalizable ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12607264/]
- 51. Outlier Treatment: Taming the Anomalies in Data [https://letsdatascience.com/outlier-treatment/]
- 52. A comprehensive performance evaluation, comparison ... [https://www.sciencedirect.com/science/article/pii/S1532046424000431]
- 53. JARVIS-Leaderboard: a large scale benchmark of ... [https://www.nature.com/articles/s41524-024-01259-w]
- 54. The How-To Guide to Data Curation in Machine Learning [https://www.lightly.ai/blog/data-curation]
- 55. Data Management 101 for drug developers: A peek behind ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10499417/]
- 56. Best Practices for Ensuring Data Quality in Clinical Trials [https://cytel.com/perspectives/best-practices-for-ensuring-data-quality-in-clinical-trials/]
- 57. Distributed denial of service (DDoS) classification based ... [https://www.nature.com/articles/s41598-025-03868-x]
- 58. A two-tier optimization strategy for feature selection in ... [https://www.nature.com/articles/s41598-025-85878-3]
- 59. Enhancing Machine Learning-Based DDoS Detection ... [https://www.mdpi.com/2079-9292/14/16/3319]
- 60. Automated drug design for druggable target identification ... [https://www.nature.com/articles/s41598-025-18091-x]
- 61. A Novel Hybrid Machine Learning Approach for DoS Attack ... [https://www.atlantis-press.com/proceedings/iccsce-25/126017533]
- 62. Enhancing drug discovery with AI: Predictive modeling of ... [https://www.sciencedirect.com/science/article/pii/S2949866X24001187]
- 63. What is the hyperparameter tuning technique for model ... [https://www.impactive-ai.com/en-insight/what-is-hyper-parameter-tuning]
- 64. Interpretability Methods in Machine Learning: A Brief Survey [https://www.twosigma.com/articles/interpretability-methods-in-machine-learning-a-brief-survey/]
- 65. Transformative Role of Artificial Intelligence in Drug ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12406033/]
- 66. 4 Methods Overview – Interpretable Machine Learning [https://christophm.github.io/interpretable-ml-book/overview.html]
- 67. LIME vs SHAP: A Comparative Analysis of Interpretability ... [https://www.markovml.com/blog/lime-vs-shap]
- 68. Extensive benchmarking of a method that estimates ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11772677/]
- 69. Leveraging External Data in the Design and Analysis of ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8893120/]
- 70. Analytical Methods for Comparing Uncontrolled Trials With ... [https://www.sciencedirect.com/science/article/pii/S1098301524028420]
- 71. A universal machine learning model for the electronic ... [https://arxiv.org/html/2508.17418v1]
- 72. Machine learned features from density of states for ... [https://www.nature.com/articles/s41467-020-20342-6]
- 73. Evaluating machine learning-based intrusion detection ... [https://www.frontiersin.org/journals/computer-science/articles/10.3389/fcomp.2025.1520741/full]
- 74. DDoS classification of network traffic in software defined ... [https://www.nature.com/articles/s41598-025-13754-1]
- 75. Better Benchmarking Improves Drug Development ... [https://www.intelligencia.ai/better-benchmarking-elevates-pharma-decision-making/]
- 76. A comparison of computational methods for expression ... [https://pubmed.ncbi.nlm.nih.gov/41250104/]
- 77. Computational transformation in drug discovery: A ... [https://www.sciencedirect.com/science/article/pii/S2949866X24000340]
- 78. Decoding disorder: Advances in predicting intrinsically ... [https://www.sciencedirect.com/science/article/pii/S157016462500030X]